Third Party Risk Management Solution for Australia
Why Australian Organizations Need TPRM Solutions
Continuously assess and monitor vendor cyber risk posture
Detect third-party exposures, data leaks, and dark web mentions
Reduce operational, reputational, and compliance risks
Ensure vendors adhere to Australian cybersecurity regulations and industry frameworks
Streamline vendor onboarding and due diligence with automated assessments
The Third-Party Risk Landscape in Australia




Key Features of Cyble’s TPRM Solution
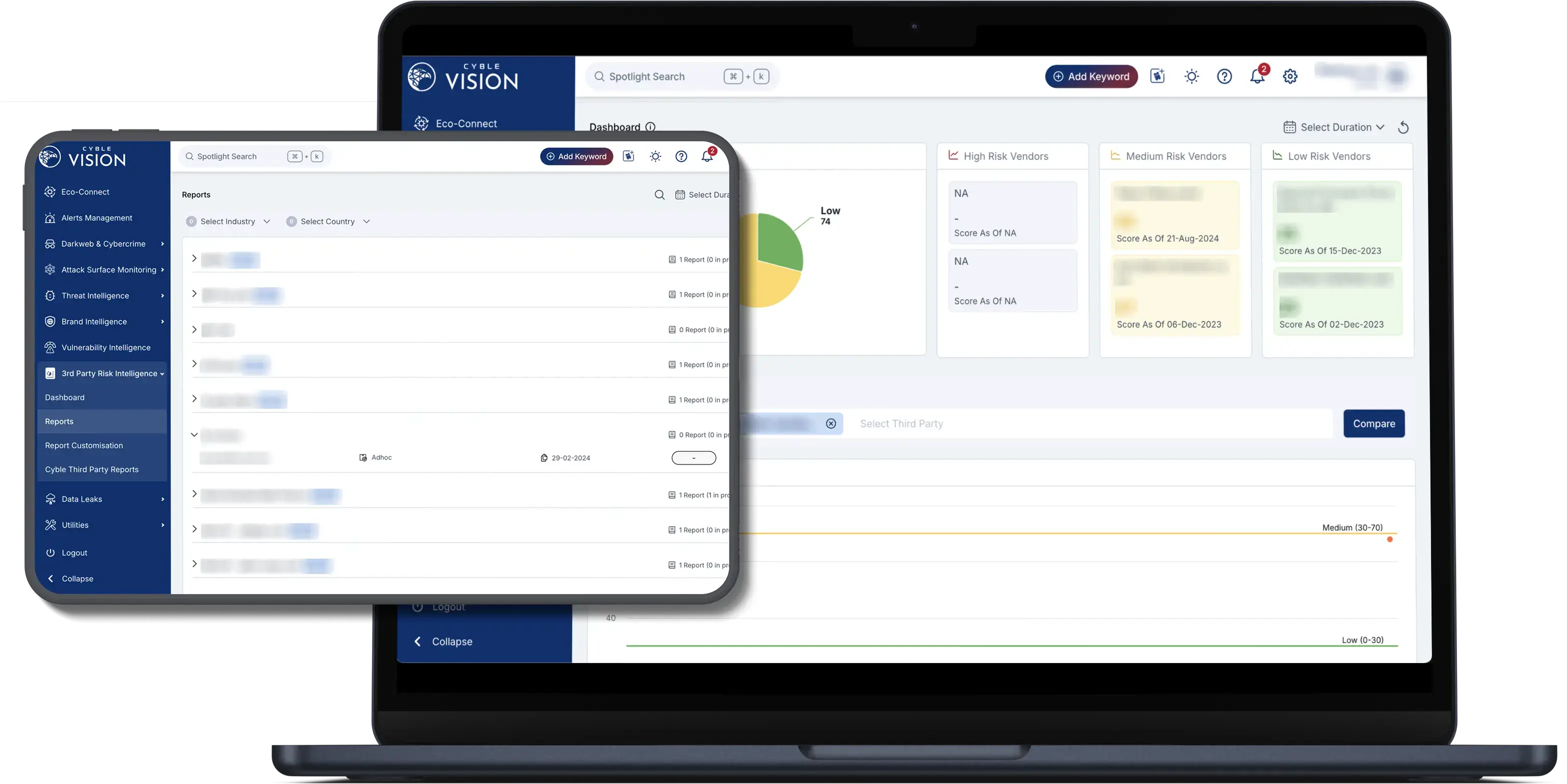
Vendor Cyber Risk Scoring
Gain real-time risk scores and threat intelligence for each vendor based on their digital footprint, vulnerabilities, and exposure.
Continuous Monitoring
Track changes in vendor risk posture through ongoing monitoring of data leaks, malware infrastructure, and dark web chatter.
Threat Intelligence Correlation
Correlate vendor-related threats with Cyble’s global intelligence feeds to identify targeted campaigns or shared infrastructure risks.
Regulatory Compliance Enablement
Meet compliance standards such as APRA CPS 234, ACSC Essential Eight, and ISO 27001 with auditable third-party risk practices.
Customizable Risk Dashboards
Prioritize and visualize vendor risks with customizable dashboards and reports aligned with your business priorities.
Recognized by Global Analyst Firms
Analysts from major research houses, industry critics, and cybersecurity leaders across the globe admire Cyble Vision’s capabilities.
Resources

Threat Landscape Report – Australia Education Sector (April 2024 – April 2025)
A Deep Dive into Cyber Threats Targeting Australia’s Education Sector Cyberattacks on Australia’s education sector is growing in both frequency and complexity. As the country’s third-largest source of income, after

Australia and New Zealand Threat Landscape Report 2024
Unveiling the Cyber Threat Landscape in Australia and New Zealand: 2024 Report Explore the evolving cybersecurity challenges and solutions in Australia and New Zealand (ANZ). This comprehensive report sheds light