Spyware is probably the stealthy but at the same time most persistent cyber threat that concerns both individuals and companies. Monitoring is the key to spyware, whereas ransomware and phishing are otherwise different. It gets into a device, tracks its activity silently, and, without any consent, gathers data. The aim is the same in case of digital spyware and common spyware software and even to advanced ones like Pegasus spyware—watch, steal, and stay hidden.
Spyware companies provide modern advanced tools with different capabilities such as capturing keystrokes, recording actions on-screen, listening conversations through the microphone, and even tracking web surfing. Some of them even masquerade as innocent applications which is one of the reasons why children learn about spyware through cartoons depicting this type of threat. Thus, it is very important for people who are using connected devices to know at least the most basic anti-spyware protection.
The danger is even greater for companies. Spying attacks can slowly draw out of the company data, financial information, and login credentials over a long time without detection. This is why firms invest in reputable antivirus spyware software and keep monitoring all the time. Some teams even go for intelligence-led platforms like Cyble to at least spot unusual behavior early and make the process of removing spyware smoothly after that.
Prior to getting into detection and protection measures, it is necessary to clarify the core definition of spyware and understand how these threats function.
Request a Demo to see how Cyble helps organizations strengthen digital defense!
Definition of Spyware
Spyware is a type of malicious software that is installed on a device without the user’s consent. It collects information secretly, sends it to third parties, and often operates without visible questions. This is the basic spyware definition, and it applies to everything from basic ad-based tracking tools to sophisticated government surveillance programs.
Common Types of Spyware
Spyware comes in various shapes and sizes, each designed to gather information without you even realizing it. While some forms of spyware are used by attackers to steal passwords or financial information, others – like Pegasus spyware – are extremely advanced, able to access messages, cameras, calls and encrypted apps without the user clicking anything.
Here are some of the most common types of spyware:
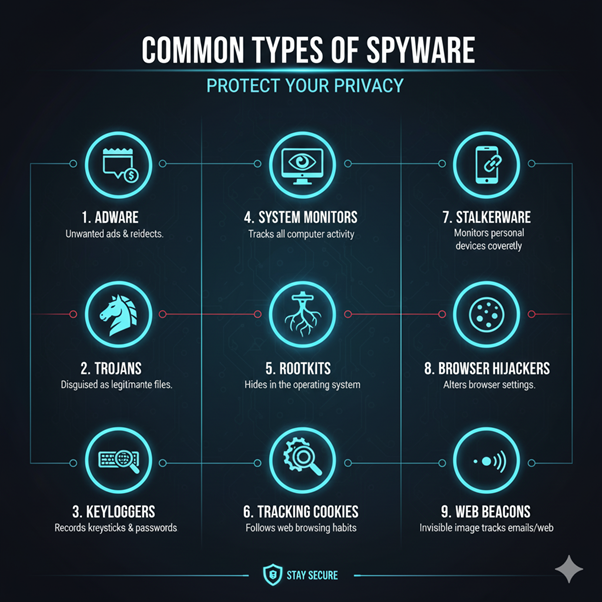
- Adware: This type of spyware bombards you with annoying pop-up ads tailored to your browsing habits. While some adware is just a nuisance, others can track your online activities extensively, posing a potential security threat.
- Trojans: These tricky programs pretend to be harmless or useful but are actually hiding malicious code. Trojans can swipe your passwords, banking information, or even give hackers a backdoor into your system.
- Keyloggers: Keyloggers are particularly dangerous as they capture every keystroke you make, whether it’s passwords, credit card numbers, chats, or emails. They are among the most frequently used and harmful types of spyware.
- System Monitors: These tools keep a close eye on your computer activity, tracking everything from login times to the apps you use, websites you visit, and even taking screenshots. Attackers utilize them to gather long-term intelligence.
- Rootkits: Rootkits dig deep into your system, making it nearly impossible to detect them or any other malicious activities. They cleverly hide processes, files, and changes from your security software.
- Tracking Cookies: These little bits of data follow you around the web, creating a profile of your browsing habits. While they are often used for marketing purposes, they can also be misused for invasive surveillance.
- Stalkerware: Stalkerware keeps an eye on mobile phones and surreptitiously tracks a person’s movements, texts, photos, and calls. It is commonly utilized in abusive partnerships or detected observation.
- Browser Hijackers: They invade your internet browser and alter settings like the homepage, cause redirects to unsafe sites, and, in some cases, even take passwords or autofill data.
- Web Beacons: These are microscopic invisible pictures that are hidden in emails or websites. Sending the notification the moment they are displayed, the sender gets to know if you have opened the message, followed a link, or gone to a page.
How Spyware Intrudes Devices
Spyware can infect a device through various entry points, some of them are:
- Fake software downloads
- Cracked or pirated applications
- Malicious email attachments
- Drive-by downloads from unsafe websites
- Infected USB devices
- Fake browser updates
- Vulnerable apps or plugins
How to Detect Spyware
One of the difficulties concerning Spyware is that it rarely displays hinting signs in an obvious way. Nevertheless, you can still monitor for red flags:
- Sudden System Slowdowns: Spyware is running behind the scenes and utilizing RAM, which results in the system experiencing delays and lag.
- Excessive Pop-ups: If there are an excessive number of ads on your system, particularly after a new app has been installed, it might be adware, or it could be digital spyware.
- High Data Consumption: The more data spyware collects from its victims, the more it has to send to the attackers, thus increasing background data usage.
- Unknown Applications: You should check the apps that are installed on your device regularly, any app that you are not familiar with may be spyware.
- Browser Redirects: If you are being redirected to weird sites while browsing, then spyware could be changing your browser settings.
- Heating and Battery Drain: In mobile devices, spyware is working non-stop, and this can result in the device getting hot or the battery draining fast.
Companies should also examine their server logs and access attempts as well as look for any unusual traffic patterns. Using a threat-intelligence platform like Cyble can assist not only in discovering these hidden signals early but also in supporting the removal of spyware processes.
Want deeper visibility into spyware threats targeting your organization? Request a demo today,
How to Get Rid of Spyware
Here are some of the methods to remove spyware from any device:
- Use Trusted Anti-Spyware Tools: Reliable anti-spyware or antivirus software can effectively scan for and remove known threats.
- Uninstall Suspicious Programs: Take a moment to check your device settings and remove any unfamiliar applications right away.
- Reset Browser Settings: Spyware often hides in browser extensions or configuration files, so resetting these can help.
- Apply Security Updates: Keeping your operating system and apps up to date can close the vulnerabilities that spyware often takes advantage of.
- Reset the Device (as a Last Resort): If all else fails, a factory reset can help reduce stubborn infections.
Organizations can also benefit from solutions like Cyble’s intelligence-driven monitoring, which helps detect suspicious behavior early and alerts teams before infections can spread.
How to Prevent Spyware Infection
Cleaning up an incident is never a good idea, especially if you can prevent it from happening in the first place. Following these guidelines will save you from spyware complications:
- Steer Clear of the Unknown: Always download your apps from approved app stores or developers you trust.
- Opt for Multi-Factor Authentication: Capturing a password does not mean that the spyware will succeed in the login, as MFA takes care of that.
- Regularly Update Systems: By applying patches the vulnerabilities that were exploited by the spyware are barred access along with the two variants of spyware.
- Implement Security Solutions: Go for an upstanding security stack that consists of spyware software detection as a part of the treated area.
- Watch Over Your Employees’ Access: Companies ought to keep an eye on unusual access patterns and device performance.
- User Awareness: The human factor is still the most important entry point for Spyware attacks.
For commercial users, Cyble’s digital-risk protection and threat-intelligence solutions provide an unobtrusive and non-promotional manner of acquiring an insight into the spyware campaigns that are developing.
Conclusion
It is not often that Spyware gets highlighted, but still, it is one of the most silent yet dangerous threats in the digital world. By knowing Spyware and the way it transmits, and spotting it early, people and businesses can cut down their risks by quite a bit. Whether it is a periodical adware or something like Pegasus that’s high-tech, the difference is in the awareness and active protection. Having the right tools, awareness, and threat-intelligence capabilities not only empowers you to keep your digital environment secure but also makes it resilient.























