Overview
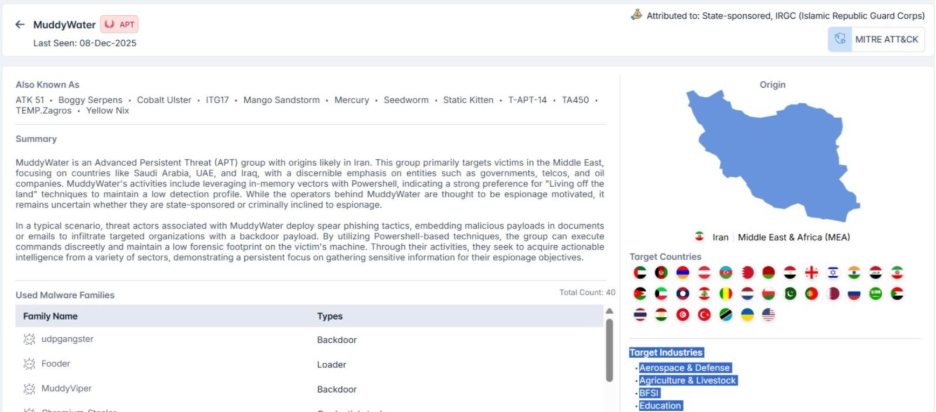
MuddyWater is an Advanced Persistent Threat (APT) group widely believed to have originated in Iran and is commonly linked to interests associated with the Islamic Revolutionary Guard Corps (IRGC). First observed several years ago, the group has maintained a consistent presence in cyber-espionage operations targeting a variety of industries and government organizations.
Unlike typical cybercriminal operations, MuddyWater is not financially motivated. Instead, the group focuses on strategic intelligence collection, maintaining a low profile while conducting operations across multiple regions and sectors. Its campaigns are characterized by stealth, persistence, and the use of legitimate tools and operating system features, which allow it to blend into normal network activity and evade detection.
Who is MuddyWater?
MuddyWater is primarily an espionage-focused APT group, specializing in covert intelligence operations rather than disruptive attacks or financial gain. Its operators rely heavily on low-visibility tactics, often leveraging native system functionalities and widely available administrative tools rather than deploying custom malware. This approach minimizes the risk of detection while allowing long-term access to targeted environments.

The group has repeatedly demonstrated technically advanced techniques for compromising third-party organizations, including spearphishing campaigns and exploiting public-facing application vulnerabilities. These operations are designed to harvest sensitive information, maintain persistence, and map critical networks over time.
While MuddyWater is widely assessed as state-aligned, particularly with Iranian strategic objectives, some ambiguity remains regarding the level of direct state control. Analysts suggest that the group may operate through a mix of formal state resources and contracted operators, giving it flexibility in execution while maintaining plausible deniability.
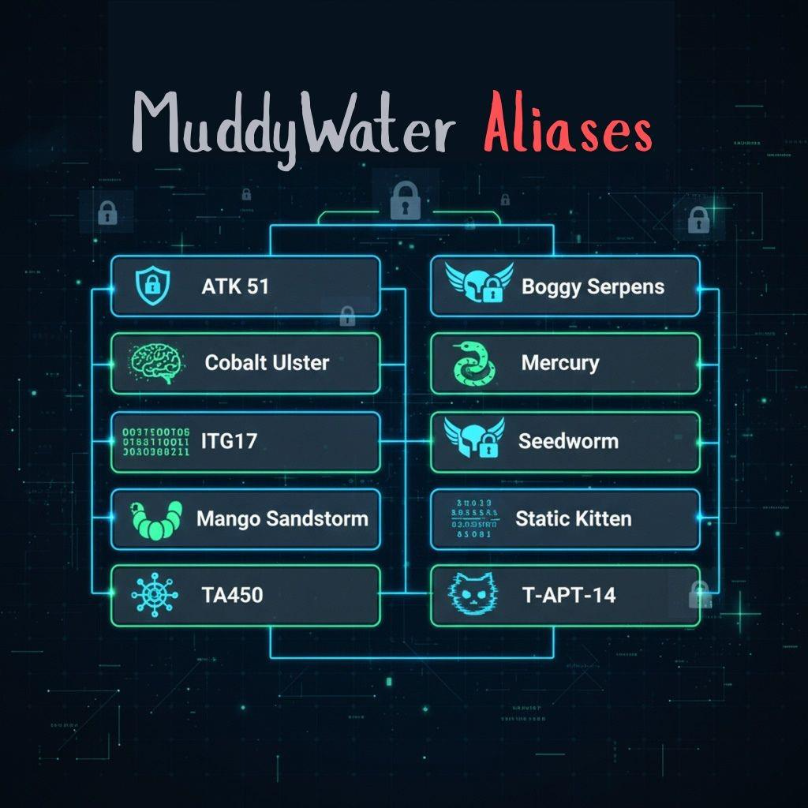
Alias Mapping for MuddyWater Group
The following list presents aliases associated with the MuddyWater group, helping analysts and researchers track their activity and campaigns across different targets.
Origin and Geographic Scope

MuddyWater’s activity is strongly concentrated in the Middle East, with additional operations observed across Europe, Africa, and parts of Asia and North America. The group demonstrates a regional priority aligned with Iranian geopolitical interests while maintaining the capability to operate globally.
Confirmed or reported target countries include, United Arab Emirates, Saudi Arabia, Iraq, Israel, Jordan, Kuwait, Qatar, Bahrain, Egypt, Sudan, Tunisia, Turkey, Afghanistan, Armenia, Azerbaijan, Georgia, Tajikistan, Laos, Thailand, India, Russia, Ukraine, Belarus, Austria, Norway, Portugal, United States, Tanzania, Mali, Northern Mariana Islands, and Iran itself.
This geographic spread indicates both regional intelligence collection and opportunistic expansion beyond immediate neighboring states.
Targeted Sectors
MuddyWater targets a wide range of industries, reflecting an interest in political, economic, military, and infrastructure-related intelligence.

The diversity of sectors suggests that MuddyWater collects intelligence not only for immediate strategic value but also for long-term situational awareness across political, economic, and societal domains.
Initial Access and Infection Chains
MuddyWater commonly gains initial access through spearphishing campaigns, exploiting both malicious attachments and embedded links. The group has demonstrated a consistent ability to compromise third-party organizations and reuse legitimate email accounts to distribute phishing messages, increasing credibility and success rates.
In addition to phishing, MuddyWater has exploited public-facing application vulnerabilities, including Microsoft Exchange memory corruption flaws, and has historically abused CVE-2017-0199, an Office vulnerability enabling remote code execution via malicious documents.
Once a victim interacts with a lure document or link, the infection chain typically delivers a lightweight loader or script-based payload that establishes an initial foothold and prepares the system for follow-on activity.
Malware Ecosystem

MuddyWater maintains a large malware arsenal, with at least 40 identified families spanning backdoors, loaders, reconnaissance tools, and credential stealers.
Key Malware Families
- UDPGangster: A UDP-based backdoor delivered through macro-enabled Word documents. UDPGangster supports remote command execution, file extraction, and staged payload delivery while incorporating extensive anti-analysis checks to evade sandbox environments.
- Fooder: A newly identified 64-bit C/C++ loader that represents a notable evolution in MuddyWater’s tooling. Fooder decrypts and reflectively loads embedded payloads, most commonly MuddyViper, entirely in memory, reducing forensic artifacts and bypassing file-based detection mechanisms.
- MuddyViper: A previously undocumented C/C++ backdoor used as a second-stage payload. Loaded via Fooder, MuddyViper operates fully in memory and supports command execution, file upload and download, credential harvesting, and browser data collection.
- Phoenix v4: A MuddyWater-linked backdoor delivered using a FakeUpdate loader. Phoenix v4 supports remote shell execution, file transfers, and process injection, using in-memory AES decryption for stealth and evasion.
- Chromium_Stealer: A credential-stealing malware that targets Chromium-based browsers, harvesting stored passwords, cookies, and session data for exfiltration to command-and-control infrastructure.
Abuse of Legitimate Tools
MuddyWater frequently repurposes legitimate administrative and reconnaissance utilities. Tools such as ChromeCookiesView, CrackMapExec, Mimikatz, LaZagne, PowerSploit, Meterpreter, ScreenConnect, and RemoteUtilities are leveraged for credential theft, lateral movement, network mapping, and persistence.
For example, ChromeCookiesView, originally designed as a legitimate browser utility, can be abused to extract session cookies and authentication tokens, enabling unauthorized access to victim accounts without needing plaintext credentials. CrackMapExec is used to enumerate Active Directory environments and facilitate lateral movement across enterprise networks.
Attack Techniques Observed
MuddyWater employs a wide range of operational methods to gain initial access to targeted environments. The group frequently takes advantage of weaknesses in internet-facing systems, allowing them to enter networks without direct user interaction.
In many cases, they rely on carefully crafted phishing campaigns, sending emails that contain either malicious attachments or deceptive links. These messages are often designed to appear legitimate and are tailored to the intended recipient, increasing the likelihood that the content will be opened and trusted.
Once access is established, MuddyWater uses several execution methods that blend into normal system activity. The group commonly relies on built-in management features and scheduling functions within operating systems to run their tools and maintain access over time.
Scripting languages and command-line interfaces are heavily used, enabling the attackers to execute commands, deploy additional components, and adapt their actions dynamically without leaving obvious traces.
MuddyWater also exploits weaknesses in client applications and encourages users to interact with malicious files or web content. By doing so, the group can trigger the execution of harmful code under the guise of legitimate activity.
These approaches allow MuddyWater to move within networks quietly, maintain persistence, and expand access while avoiding detection mechanisms that are designed to identify more overt or noisy forms of malware.
Conclusion
As of late 2025, MuddyWater continues to operate as a persistent and capable espionage-focused threat actor, demonstrating a sustained emphasis on stealth, long-term access, and disciplined operational security. The group’s consistent use of covert techniques, reliance on trusted system components, and steady evolution of its tooling reinforce its role as a strategic intelligence collection actor rather than a short-lived cybercriminal entity.
Its wide geographic reach and continued focus on government, energy, and telecommunications organizations, particularly across the Middle East, mean that affected sectors remain at elevated risk from ongoing and future campaigns. Against this backdrop, intelligence-driven visibility is critical.
Through its threat research and AI-powered intelligence capabilities, Cyble helps organizations track actors like MuddyWater, understand new tactics, and respond proactively to cybersecurity risks. Security teams seeking deeper insight into state-aligned threats and improved preparedness can explore Cyble’s threat intelligence capabilities by scheduling a demo or requesting an external threat assessment report.
Recommendation and Mitigation Strategies
- Enhance Email Security: Use advanced phishing detection and regularly train employees to recognize malicious emails, especially those appearing to come from trusted sources.
- Secure Public-Facing Systems: Promptly patch and harden internet-facing applications to reduce the risk of exploitation.
- Control Script and Tool Usage: Restrict and monitor the use of scripting engines and built-in administrative tools commonly abused for stealthy execution.
- Strengthen Endpoint Monitoring: Deploy behavior-based endpoint detection to identify abnormal activity and misuse of legitimate tools.
- Limit Privileged Access: Apply least-privilege principles and strong authentication to reduce the impact of credential compromise.
- Monitor Internal Network Activity: Watch for signs of lateral movement, credential abuse, and unauthorized system discovery.
- Leverage Threat Intelligence: Use current threat intelligence to track evolving MuddyWater tactics and adjust defenses proactively.
MITRE ATT&CK Techniques Associated with the MuddyWater

- Exploit Public-Facing Application (T1190): MuddyWater has exploited vulnerabilities in internet-facing systems, including a Microsoft Exchange memory corruption flaw, to gain initial access without direct user interaction.
- Spearphishing Attachment (T1566.001): The group has compromised third-party organizations and abused legitimate email accounts to send spearphishing messages containing targeted malicious attachments.
- Spearphishing Link (T1566.002): MuddyWater has distributed targeted phishing emails with embedded malicious links designed to lure victims into interacting with harmful content.
- Windows Management Instrumentation (T1047): MuddyWater has leveraged WMI through its malware to execute payloads and collect host-level information while blending into normal system activity.
- Scheduled Task (T1053.005): The group has created scheduled tasks to maintain persistence and ensure the continued execution of its tools within compromised environments.
- PowerShell (T1059.001): MuddyWater has extensively used PowerShell to execute commands, download payloads, and manage post-compromise activity.
- Windows Command Shell (T1059.003): The threat actor has used custom tooling to establish reverse shells and execute commands through the Windows command-line interface.