Mustang Panda, also known across security reporting as Bronze President, Camaro Dragon, CeranaKeeper, Earth Preta, HoneyMyte, PKPLUG, Red Lich, Stately Taurus, and TEMP.Hex is one of the most active and persistent China-based espionage groups operating in 2025.
Intelligence assessments consistently associate the group with state-directed objectives, primarily focused on political, governmental, and strategic sectors. While Mustang Panda operates worldwide, long-term monitoring reveals a disproportionately heavy focus on Mongolia, alongside extensive activity targeting the Asia-Pacific, Europe, Africa, and North America.
Overview and Strategic Objectives
The group’s operations follow a consistent pattern centered on intelligence collection, long-term access, and exploitation of high-value organizations. Mustang Panda frequently relies on spearphishing to deliver customized malware families such as PlugX and Poison Ivy, using these tools to establish footholds inside targeted systems before expanding laterally.
Typical operations begin with a tailored email containing either a malicious attachment or a link directing the victim to an archive hosted on platforms such as Google Drive or Dropbox. These delivery mechanisms often carry legitimate-looking executable files paired with malicious DLLs designed to load stealthy backdoors or reconnaissance modules.
Geographic Focus and Primary Sectors of Interest

Mustang Panda targets a wide array of countries. Confirmed victimology includes entities in Australia, Bangladesh, Belgium, Bulgaria, China, Cyprus, Czech Republic, Germany, Ethiopia, France, the United Kingdom, Greece, Hong Kong, Hungary, Indonesia, India, Japan, South Korea, Myanmar, Mongolia, Nepal, the Philippines, Pakistan, Russia, Sweden, Singapore, Slovakia, South Sudan, Thailand, Taiwan, the United States, Vietnam, and South Africa.
The threat actor focuses on organizations that provide geopolitical, military, or sensitive internal information. Documented targeted sectors include:
- Aerospace and Defense
- Education
- Government and Law Enforcement Agencies
- Healthcare
- Telecommunications
These industries align with long-term intelligence collection goals, including monitoring political developments, assessing foreign defense postures, and gathering sensitive research or communications.
Operational Toolset
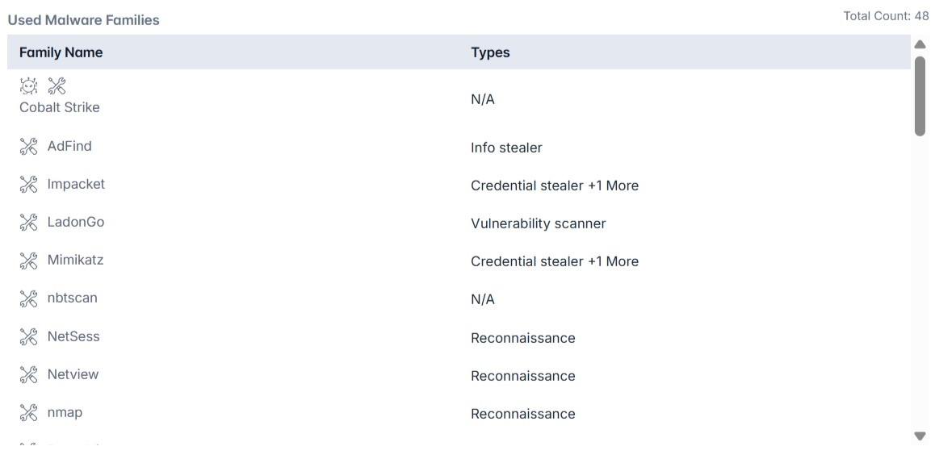
Mustang Panda’s toolkit is extensive and diverse, combining custom malware families, open-source utilities, and widely known credential theft frameworks. Their known arsenal includes:
- Backdoors: 9002 RAT, Bookworm, CANONSTAGER, DOPLUGS, Farseer, Hodur, RCSession, TinyNote, TONESHELL, WispRider
- Loaders / Droppers: HopperTick, MISTCLOAK, Orat, PUBLOAD, SplatDropper, TONEINS
- Reconnaissance Tools: AdFind, NetSess, Netview, nmap, PowerView, PVE Find AD Users, PlugX (also used for reconnaissance), THOR, Zupdax
- Credential Theft Tools: Impacket, Mimikatz, DCSync, Hdump
- Backdoor / Shell Utilities: TeamViewer, China Chopper
- Other Components: nbtscan, Wevtutil, WmiExec, SnakeDisk (worm capability), STATICPLUGIN, CorKLOG, PAKLOG, HenBox (info stealer)
In addition to their own malware, Mustang Panda frequently utilizes legitimate administrative software or security products to execute side-loading attacks.
Access, Execution, and Persistence Techniques
Mustang Panda commonly gains entry into target environments by sending emails that contain harmful attachments or links, often disguised within archive files or hosted on cloud services, which lure recipients into opening content that secretly installs their tools.
Once they obtain a foothold, the group relies on a broad mix of methods to run their payloads, including scripts, scheduled tasks, document-based tricks, web content, and repurposed legitimate software that helps them blend into normal system activity.
They also utilize various programming and automation features within operating systems to conceal their actions and ensure their tools continue running after the initial infiltration.
To remain planted within compromised networks, Mustang Panda employs a variety of persistence mechanisms, including placing startup entries in system settings, hiding behind legitimate applications, deploying lightweight web-based access points, and utilizing techniques that enable their components to activate only under specific conditions.
Conclusion
As of mid-2025, Mustang Panda continues to operate as a highly capable state-aligned threat group with a global reach, consistently targeting government agencies, defense contractors, telecommunications providers, and academic institutions. Their campaigns rely on sophisticated phishing methods, custom malware, and strategic use of legitimate tools to maintain long-term access and conduct intelligence operations.
Cyble’s threat intelligence capabilities provide visibility into persistent espionage threats, helping organizations detect, monitor, and respond to emerging risks in real-time. Book a free demo or start a free external threat assessment to uncover exposed assets, track threat actors like Mustang Panda, and strengthen your organization’s cyber resilience.
Recommendation and Mitigation Strategies
- Strengthen Email Security: Implement advanced email filtering and anti-phishing solutions to block malicious attachments and links. Encourage staff to verify unexpected emails and provide regular phishing awareness training to ensure a secure environment.
- Patch and Harden Systems: Regularly update operating systems, applications, and network devices to remediate known vulnerabilities. Prioritize critical systems, including government, defense, and telecommunications platforms.
- Restrict Script Execution: Control the execution of scripts, macros, and other automated code. Enforce policies for signed scripts, disable unnecessary scripting engines, and monitor PowerShell, VBScript, and JavaScript usage to ensure optimal security.
- Monitor for Abnormal Activity: Deploy endpoint detection and response (EDR) and network monitoring to identify unusual behavior, such as unexpected scheduled tasks, lateral movement, or attempts to manipulate registry keys.
- Control Administrative Privileges: Limit administrative rights and implement role-based access control to reduce the risk of credential misuse. Enforce multi-factor authentication (MFA) for all remote and privileged accounts.
- Protect Web and Cloud Assets: Scan for exposed web shells, misconfigured cloud storage, and publicly accessible sensitive files. Ensure proper access controls and monitor for unusual access patterns.
- Backup and Recovery: Maintain offline, encrypted backups of critical systems and data. Test restoration procedures regularly to minimize disruptions in the event of a compromise.
- Threat Intelligence Integration: Leverage real-time threat intelligence, such as from Cyble, to track Mustang Panda activity, identify new TTPs (tactics, techniques, and procedures), and proactively defend against targeted campaigns.
- Incident Response Preparedness: Develop and regularly update incident response plans, including specific protocols for espionage-focused intrusions and persistence-based malware, ensuring rapid containment and remediation.
MITRE ATT&CK Techniques Associated with the Mustang Panda
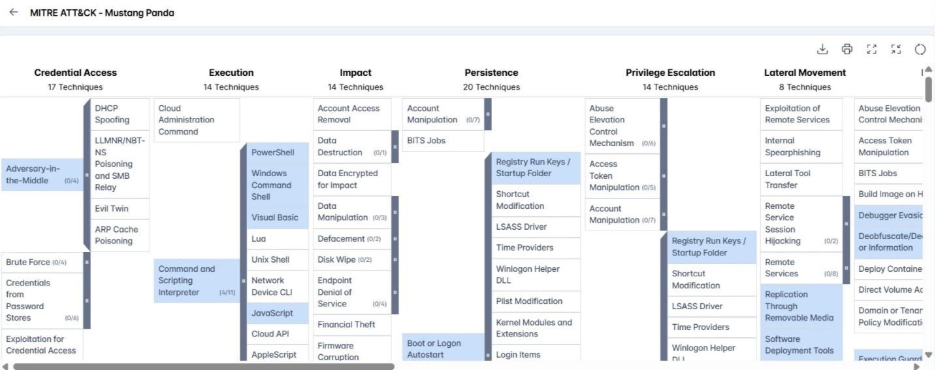
- Spearphishing Attachment (T1566.001): Mustang Panda uses spearphishing emails containing RAR or ZIP archives that bundle legitimate executables with malicious DLLs. These attachments were central to the RedDelta Modified PlugX Infection Chain for gaining initial access.
- Spearphishing Link (T1566.002): The group sends phishing emails with embedded links that direct victims to malicious archives hosted on platforms like Google Drive or Dropbox. In RedDelta operations, these links led to HTML pages that fingerprinted the victim’s system and delivered malicious MSC files.
- Windows Management Instrumentation (T1047): Mustang Panda executes malicious PowerShell scripts through WMI to run payloads and support follow‑on activity.
- Scheduled Task (T1053.005): The group creates scheduled tasks to launch malware, maintain persistence, and establish reverse shells for long‑term access.
- Command and Scripting Interpreter (T1059): Mustang Panda has used various scripting interpreters, including the deployment of Meterpreter shellcode for execution.
- PowerShell (T1059.001): The group uses malicious PowerShell scripts and relies on LNK files to trigger PowerShell commands that install payloads such as PlugX, as observed in RedDelta activity.
- Windows Command Shell (T1059.003): Mustang Panda executes HTA files, batch scripts, and command-line instructions, including commands designed to delay execution before launching malware.
- Visual Basic (T1059.005): The group embeds VBScript in LNK files to enable downloads and collection, uses malicious VBA macros in documents, and employs VBS-based persistence via “autorun.vbs” placed in startup folders.
- JavaScript (T1059.007): Mustang Panda executes JavaScript payloads using wscript.exe to run malicious scripts on target systems.
- Software Deployment Tools (T1072): Legitimate enterprise tools, including antivirus and security agents, are abused to run scripts and side‑load malicious DLLs.
- Native API (T1106): The group makes extensive use of Windows API calls for execution and evasion.
- Shared Modules (T1129): DLLs are loaded using functions like LoadLibrary to support execution chains.
- Exploitation for Client Execution (T1203): Mustang Panda exploits vulnerabilities such as CVE‑2017‑0199 and uses techniques like GrimResource to weaponize MSC files for arbitrary code execution.
- Malicious Link (T1204.001): The group sends links to malicious webpages that deploy JavaScript-based droppers. In some cases, these links trigger MSC files that execute PowerShell commands to retrieve remote MSI installers.
- Malicious File (T1204.002): User‑executed malicious files, including LNK objects and executables showing tailored decoy documents, are used to deliver malware during campaigns like those linked to RedDelta.
- Traffic Signaling (T1205): Mustang Panda uses “magic packet” values in command‑and‑control communication, activating in-memory components only when specific packet patterns are detected.