NoName057(16), also referenced as 05716nnm, Nnm05716, NoName057, and NoName05716, is a pro-Russian hacktivist group that emerged in early 2022. The group quickly became known for coordinating large-scale Distributed Denial of Service (DDoS) operations against governments, critical infrastructure, and private-sector organizations in countries viewed as opposing Russian geopolitical interests. Its activity is ideologically motivated rather than financially driven, and its operations often coincide with political developments related to Russia’s war against Ukraine.
Since its first observed campaigns, NoName057(16) has used Telegram as its primary communication channel, providing updates on targets, circulating propaganda, and mobilizing volunteers who participate in coordinated attacks. The group also relies on its custom DDoS toolkit, DDOSIA, which streamlines the execution of high-volume traffic floods. Through these combined methods, NoName057 has positioned itself as one of the more persistent hacktivist collectives operating within the wider pro-Russian ecosystem.
By mid-2025, intelligence reporting suggested that some former members of the People’s Cyber Army, an entity historically associated with APT44, had aligned themselves with NoName057(16). If accurate, this shift likely enhanced the group’s operational maturity, strengthening its ability to conduct attacks that extend beyond basic hacktivism.
Geographic and Industry Targeting

Although the group’s ideological focus remains centered on Ukraine, NoName057 campaigns have reached far beyond the region. Targets have been recorded across Europe, North America, and parts of Asia. Countries repeatedly affected include Canada, the Czech Republic, Germany, Denmark, Estonia, Spain, France, the United Kingdom, Israel, Italy, South Korea, Lithuania, Latvia, Moldova, Norway, Poland, Turkey, Taiwan, Ukraine, and the United States.
Sector-specific targeting by NoName057 spans a wide variety of industries. The group has directed attention toward agriculture, banking and financial services, consumer goods, energy and utilities, government agencies, law enforcement, hospitality, manufacturing, telecommunications, retail, transportation, and logistics.
This pattern aligns with the behavior of ideologically motivated actors seeking to create public disruption and generate media attention rather than stealing data or achieving persistence within affected networks.
Tooling and Related Groups

NoName057 campaigns frequently incorporate tools and infrastructure provided by the associated group known as Dosia. While Dosia is sometimes considered a separate entity, its capabilities are frequently leveraged by threat actors aligned with pro-Russian causes, including NoName057. Dosia’s activities center on social engineering and DDoS operations, and it has been linked to infrastructure initially tied to the obscure hosting provider Stark Industries Solutions.
Dosia’s ongoing development of DDoS utilities, reported to be increasingly compatible with diverse processor architectures and operating systems, suggests an effort to make its tools more accessible to a distributed volunteer base. Threat actors using Dosia-linked resources often rely on deception tactics to trick users into exposing sensitive information or unknowingly assisting malicious operations.
Tactics and Techniques
NoName057 typically begins its operations by taking advantage of weaknesses in systems that are accessible online, using flaws or outdated components to gain a foothold and sometimes hiding its activity once inside.
Their primary method of disruption involves overwhelming networks with excessive traffic to knock out websites, email platforms, and other online services offline, often as a way to send a political message or support a broader narrative. They also carry out attacks that directly overload or destabilize individual devices, causing them to crash or become unresponsive without flooding the entire network.
Before launching these actions, NoName057 gathers information about potential targets, such as user details or system characteristics, sometimes by probing online services or planting malicious content on compromised sites, allowing them to tailor and strengthen their attacks.
Recent Disruption: Operation Eastwood
Between 14 and 17 July 2025, Europol and Eurojust coordinated Operation Eastwood, a major effort to suppress the infrastructure supporting NoName057(16). Law enforcement agencies across more than a dozen countries dismantled over 100 servers linked to the group, disrupting command channels and taking core systems offline. Investigators issued seven arrest warrants and conducted numerous searches and interviews targeting suspected collaborators.
Authorities also contacted more than 1,000 individuals believed to have supported the group’s campaigns, informing them of potential legal consequences. Prior investigations had shown that NoName057 frequently relied on crowdsourced participation, sometimes offering small cryptocurrency rewards to encourage involvement.
Conclusion
As of 2025, NoName057(16) continues to operate as a highly active pro-Russian hacktivist collective, targeting governments and organizations that oppose Russia’s strategic interests. Its volunteer-driven ecosystem, coordination with groups like Dosia, and continuous adaptation of attack techniques allow it to remain effective despite recent law-enforcement disruptions.
To counter fast-moving threats like this, Cyble’s External Threat Profile Report offers organizations a clear view of vulnerabilities, misconfigurations, data leaks, and dark-web exposure.
Get a free External Threat Assessment to understand your exposure and take corrective action. Or schedule a personalized demo to see how Cyble can protect your organization against NoName057(16) and other threat actors today!
Recommendation and Mitigation Strategies
- DDoS Protection: Deploy traffic filtering, rate limiting, and redundant infrastructure to withstand high-volume attacks.
- Secure Public-Facing Systems: Regularly patch web servers, databases, and network devices to prevent exploitation.
- Endpoint Hardening: Monitor system resources, apply updates, and use endpoint detection to prevent crashes or service disruptions.
- Staff Awareness: Train employees against social engineering and phishing campaigns commonly used by NoName057 and Dosia.
- Threat Intelligence & Monitoring: Use continuous monitoring and tools like Cyble’s External Threat Profile Report to detect vulnerabilities, exposed data, and suspicious activity.
MITRE ATT&CK Techniques Associated with the NoName057(16)
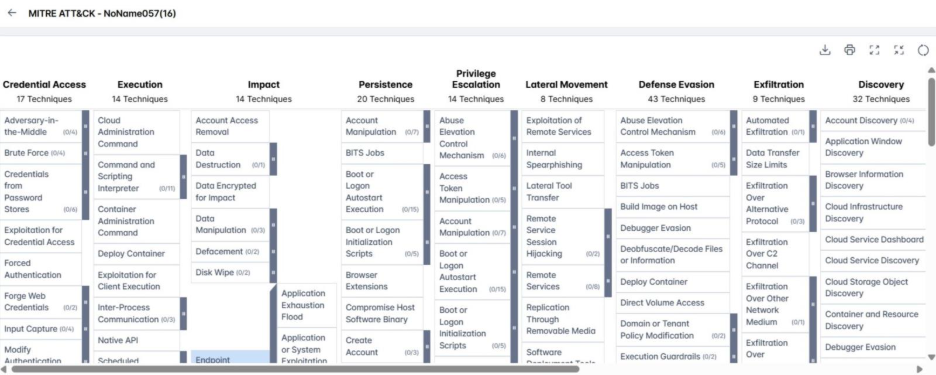
- Exploit Public-Facing Application (T1190): Adversaries target internet-facing systems, including websites, databases, network devices, and cloud/container infrastructure, exploiting software bugs, misconfigurations, or outdated components to gain initial access.
- Network Denial of Service (T1498): Attackers overwhelm network bandwidth to disrupt websites, email, DNS, or web services, using single or distributed sources, often leveraging IP spoofing or botnets.
- Endpoint Denial of Service (T1499): Adversaries exhaust system resources or crash services on target devices without saturating the network, targeting OS, server apps, and application layers, sometimes using botnets or traffic manipulation.
- Gather Victim Identity Information (T1589): Attackers collect personal data, credentials, and user details via phishing, system probing, or publicly available sources to support further attacks.
- Gather Victim Host Information (T1592): Adversaries gather configuration and administrative details of target systems through scanning, phishing, or embedding malicious content, aiding in reconnaissance and operational setup.