Overview
Putter Panda is a Chinese state-sponsored threat group linked to Unit 61486 of the 12th Bureau of the People’s Liberation Army (PLA) 3rd General Staff Department (GSD). First observed conducting operations in 2007, the group has maintained persistent cyberespionage campaigns against strategic targets worldwide. Its activities were last documented on 17 July 2025.
Putter Panda is known under several aliases, including 4HCrew, APT 2G0024, Group 36, MSUpdater, SearchFire, Sulphur, and TG-6952. Despite the variety of names, all are linked by consistent tactics, targeting patterns, and malware families.
The group’s operations have primarily focused on government agencies, contractors, and research organizations, with a particular emphasis on the space and satellite industry in Europe, the United States, and Japan.
Operational Focus and Targeting
Putter Panda’s campaigns exhibit an espionage-oriented objective, seeking sensitive technical and governmental information. Research conducted by cybersecurity firms, including CrowdStrike, highlights the group’s interest in aerospace and defense, government and law enforcement, and high-tech research sectors.
The group’s targeting strategy combines spear-phishing emails with sophisticated social engineering tactics. In some campaigns, Putter Panda has sent seemingly innocuous materials, such as a fake yoga brochure, to lure victims into opening malicious attachments. These campaigns are carefully tailored to the operational context and cultural norms of the target region, increasing the likelihood of successful compromise.
Malware Arsenal

Putter Panda employs a limited but effective set of malware families, each serving distinct operational purposes. The known families include:
- 3PARA RAT: A C++-based Remote Access Trojan (RAT) capable of operating as a DLL or executable. It allows the threat of actors to gain unauthorized access, exfiltrate sensitive information, deploy additional malware, and maintain persistent control over compromised systems.
- 4H RAT: Another backdoor tool, providing similar capabilities in terms of remote control and data exfiltration.
- Httpclient: A lightweight malware tool primarily used for establishing covert communications with command-and-control (C2) servers. HttpClient checks connectivity to legitimate websites (e.g., http://www.microsoft.com) before connecting to its designated C2 endpoint, indicating a secondary or backup role in campaigns.
- MSUpdater: A Trojan designed to masquerade as a legitimate Microsoft Windows Update process. This malware is VM-aware and employs encoded HTTP communication with its C2 server. MSUpdater can upload, download, and execute files remotely, evading sandbox detection by appearing as a trusted system process.
- PNGDowner: A straightforward “download-and-execute” malware developed in C++. It performs connectivity checks and extracts proxy credentials, when necessary, then retrieves and executes more complex payloads. Unlike 3PARA RAT or MSUpdater, PNGDowner does not maintain persistence on the target system.
Together, these tools enable Putter Panda to maintain a flexible and adaptive attack capability, coordinating initial access, persistence, and exfiltration.
Tactics and Techniques
Putter Panda’s operations follow established cyberattack methodologies, focusing on persistence, privilege escalation, and defense evasion. To maintain a foothold on compromised systems, the group’s malware often installs itself into the Windows registry, ensuring it executes automatically each time the system starts. This approach allows their tools to remain active over extended periods, even after system reboots.
In addition to maintaining persistence, Putter Panda frequently escalates its privileges by injecting malicious code into network-enabled processes such as email clients and web browsers. This technique grants attackers elevated access to sensitive system functions, enabling them to interact with key applications and extract valuable information without immediate detection.
The group also prioritizes stealth through sophisticated defense evasion methods. Their malware payloads are routinely obfuscated using encryption or simple encoding techniques, making analysis and detection more difficult. In some cases, the malware actively targets security software, attempting to disable antivirus processes to reduce the risk of discovery.
Together, these strategies demonstrate Putter Panda’s focus on long-term access, operational security, and covert data collection. By combining persistence, privilege escalation, and defense evasion, the group can conduct sustained surveillance and exfiltrate sensitive information across multiple campaigns while minimizing the likelihood of detection.
Attack Flow
A typical Putter Panda intrusion begins with a targeted spear-phishing email. Once a recipient opens the malicious file attached, a dropper such as MSUpdater or PNGDowner installs the RAT (e.g., 3PARA) or additional backdoor components.
The malware establishes a secure, encoded communication channel with the C2 infrastructure, often appearing as routine network traffic. From there, operators can remotely control the compromised system, exfiltrate sensitive data, and deploy secondary payloads as needed.
This method allows Putter Panda to operate covertly within targeted networks for extended periods, gathering intelligence without detection.
Conclusion
Putter Panda is a state-sponsored cyberespionage actor with a long operational history. Its combination of targeted social engineering, stealthy malware, and advanced persistence techniques makes it a threat to government agencies, research organizations, and critical infrastructure sectors.
Organizations operating in sensitive industries must prioritize vigilance, adopt layered cybersecurity defenses, and collaborate across sectors to detect, mitigate, and prevent such persistent threats effectively.
Platforms like Cyble provide essential capabilities in this fight, offering intelligence-driven, AI-native solutions that empower organizations to stay ahead of modern-day threats. With tools such as Cyble Vision, Hawk, and Blaze AI, security teams gain real-time threat intelligence, autonomous detection, and proactive defense mechanisms.
Cyble’s platforms can monitor dark web activity, identify vulnerabilities, and automate threat responses, enabling organizations to anticipate attacks before they happen and respond with precision.
Don’t wait for the next attack to hit. Cyble’s AI-native, intelligence-driven platform empowers organizations to detect, predict, and neutralize threats in real time. From monitoring the dark web to scanning your attack surface, Cyble provides autonomous threat hunting, automated response, and actionable intelligence, all in one unified platform.
Act before attackers do. Schedule a free demo today and experience how Cyble’s cutting-edge solutions, Vision, Hawk, Blaze AI, and more, keep your systems secure, your data protected, and your operations resilient. Stay one step ahead, always.
Recommendations and Mitigations
- Enhance Email Security & Awareness: Deploy advanced email filters and conduct regular phishing simulations to reduce initial access risk.
- Use Endpoint Detection and Response (EDR) to monitor for unusual processes, registry changes, and covert communications.
- Enforce Least Privilege & MFA: Limit user privileges, monitor admin accounts, and require multi-factor authentication.
- Apply Multi-Layered Defenses: Combine antivirus, firewalls, IDS/IPS, and behavioral analytics to detect stealthy malware.
- Continuous Network Monitoring: Track unusual outbound traffic and C2 communications for early threat detection.
- Regular Patch & Vulnerability Management: Scan for vulnerabilities and apply timely updates to reduce exploitable entry points.
- Segment Networks & Control Data Flow: Limit lateral movement and use DLP systems to prevent data exfiltration.
- Leverage Threat Intelligence Platforms: Use Cyble Vision, Hawk, or Blaze AI for real-time monitoring, autonomous response, and predictive threat intelligence.
- Prepare & Test Incident Response Plans: Maintain playbooks, conduct exercises, and ensure readiness for rapid containment.
- Collaborate & Share Threat Intelligence: Participate in ISACs and industry reporting to stay informed of cyber threats.
MITRE ATT&CK Techniques Associated with Putter Panda
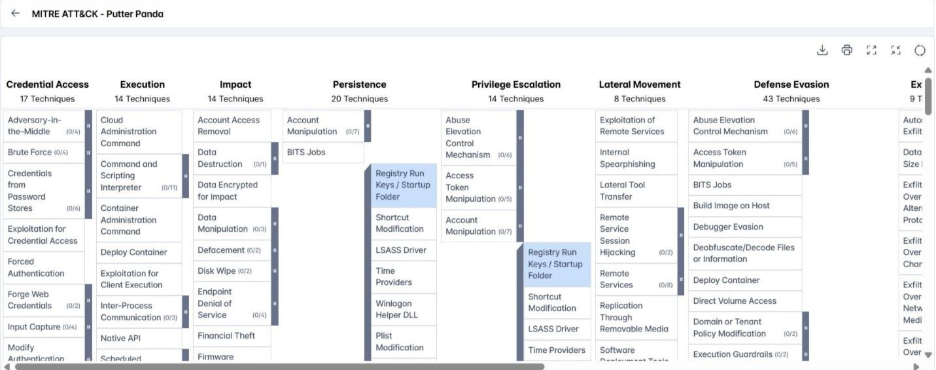
- Registry Run Keys / Startup Folder (T1547.001): A dropper used by Putter Panda installs itself into the Windows registry at HKCU\Software\Microsoft\Windows\CurrentVersion\Run with a value named McUpdate.
- DLL Injection (T1055.001): Executables dropped by Putter Panda inject specified DLLs into network-enabled processes, including Outlook, Outlook Express, Internet Explorer, and Firefox, to gain elevated access.
- Encrypted/Encoded Files (T1027.013): Droppers use RC4 encryption or a 16-byte XOR key (0xA0–0xAF) to obfuscate malware payloads and avoid detection.
- Disable or Modify Tools (T1562.001): Malware attempts to terminate security processes to reduce the chance of discovery.