TA428 is a persistent threat actor first identified in March 2019. The cluster has been linked to multiple operations, including Operation “LagTime IT,” Operation “StealthyTrident,” and the activity tracked as PandaThunderCats, and was last observed on 19‑Sep‑2025. Analysis of its campaign points to a focus on espionage‑oriented intrusions against government and related targets in the Asia-Pacific region and beyond.
TA428 has targeted government and law enforcement entities as well as manufacturing organizations. Recorded victim countries include Afghanistan, Belarus, Yemen, Myanmar, Russia, Ukraine, and the United Arab Emirates.

The group has repeatedly used culturally and regionally tailored lures, for example, IT‑themed decoys aimed at East Asian targets, and carried out spear‑phishing campaigns that mimic common local names and use adversary‑controlled free email accounts (notably yahoo[.]co[.]jp and yahoo[.]com) as sender domains.
Operational Behavior and Collaborations
TA428 has been observed collaborating and sharing infrastructure or tradecraft with other clusters. Notably, it has been involved in Operation StealthyTrident and has operational overlap or collaboration with actors tracked as Emissary Panda, APT27, LuckyMouse, and Bronze Union. TA428 campaigns historically used spear‑phishing with malicious RTF attachments and lures localized to the languages and operational concerns of targeted entities.
Malware and Tooling

The group’s activity has been associated with a modest set of malware families (total count: 6). Known families and roles include 8.t Dropper, Albaniiutas, Cotx RAT, CoughingDown, Poison Ivy, and nccTrojan.
Cotx RAT
Cotx RAT is a core component of several TA428 campaigns. Technical characteristics reported include:
- Implementation in C++.
- Malicious code hidden inside a DLL named RasTls.dll.
- Configuration data encrypted and stored in a PE section labeled “.cotx” inside the DLL and also placed in the Windows registry under HKEY_LOCAL_MACHINE\SOFTWARE\Intel\Java\user.
- Network communications use TLS encryption and a proxy‑aware command‑and‑control architecture.
- On compromise, Cotx RAT typically beacons system metadata (computer name, username, Windows version, etc.) to its C2 infrastructure. Reported behaviors include remote command execution, data collection and exfiltration, and persistence for long‑term access.
TA428 has also employed Poison Ivy and droppers; some campaigns show overlap in command‑and‑control infrastructure between Poison Ivy and Cotx RAT families, and some operators have used shared payload distribution techniques (for example, spear‑phishing with weaponized documents).
Other families/context
- nccTrojan: reported active since at least 2018 and primarily associated with targeting in South Korea. It is a custom RAT used for information theft and persistent surveillance; distribution has commonly occurred via spear‑phishing attachments or links. Links between nccTrojan and other families (Kimsuky, BabyShark) have been noted in open reporting.
- CoughingDown: described in the source material with limited public detail; attribution, capabilities and exact usage scenarios remain unspecified in the available dataset.
Tactics and Techniques
TA428’s operations reflect common intrusion strategies that emphasize system access, user manipulation, and long-term persistence within targeted environments.
One of the group’s primary methods involves exploiting vulnerabilities in software used by their targets. These vulnerabilities are typically found in everyday applications like web browsers, office suites, or widely deployed third-party tools. By exploiting these weaknesses, TA428 is able to execute malicious code on a victim’s system, often without requiring any direct interaction from the user. In several campaigns, the group has embedded malicious code into documents, which activates once opened.
Social engineering plays an important role in TA428’s Tactics. The group frequently relies on carefully crafted phishing emails that appear to come from legitimate sources familiar to the target. These emails often contain malicious documents or links that, when opened, initiate the infection process. In some cases, the group leaves harmful files in shared folders or on user desktops, relying on curiosity or routine behavior to trigger the malware.
Once access is gained, TA428 works to maintain a long-term presence within the compromised system. One way they do this is by configuring infected software to automatically run every time a computer starts up or a user logs in. This ensures that their tools remain active even after system reboots, allowing them to maintain control and continue their operations undetected.
Malware Distribution and Typical Attack Flow
A common scenario begins with a spear‑phishing email sent from an adversary‑operated free mail account that imitates a local sender. The bait contains an RTF or Office document exploiting a client’s vulnerability or requiring the user to open the attachment.
Successful execution drops a loader or dropper, which installs a RAT (such as Cotx) hidden in RasTls.dll and registers configuration in the registry. The implant then establishes TLS‑protected communication with a proxy‑aware C2, beacons host details and awaits commands to collect or exfiltrate sensitive data.
Conclusion
TA428 represents a mature and coordinated threat actor with a clear focus on cyber espionage. Its consistent use of spear-phishing, exploitation of client-side vulnerabilities, and deployment of customized malware, particularly Cotx RAT, demonstrates a well-developed approach to achieving long-term access and data exfiltration.
The group’s choice of targets, which includes government entities and strategic industries across multiple countries, further supports its alignment with state-level intelligence objectives. With documented collaborations and infrastructure overlaps involving other China-attributed groups, TA428 appears to operate within a broader ecosystem of aligned threat actors.
To stay ahead of threat actors like TA428, organizations must adopt proactive, intelligence-driven defense strategies. Cyble’s AI-native security platform — powered by Blaze AI — delivers predictive threat intelligence, autonomous threat hunting, and real-time response capabilities to help you outpace evolving adversaries.
Book a free demo with Cyble today and discover how our platform can secure your environment against advanced persistent threats.
Schedule Your Demo
Recommendations and Mitigations
- Use secure email gateways to detect and block spear-phishing emails with malicious attachments or links.
- Disable or restrict macros in Office documents to prevent malware execution via phishing attachments.
- Regularly patch software and applications to close vulnerabilities commonly exploited by TA428.
- Monitor the use of system tools like PowerShell, PsExec, and rundll32 for signs of malicious activity.
- Detect and block persistence mechanisms by auditing registry keys, scheduled tasks, and startup entries.
- Segment networks and enforce least privilege to limit lateral movement and access to critical systems.
- Integrate threat intelligence feeds to identify and respond to known TA428 indicators of compromise.
- Provide phishing awareness training and run simulations to improve user resistance to social engineering.
MITRE ATT&CK Techniques Associated with TA428
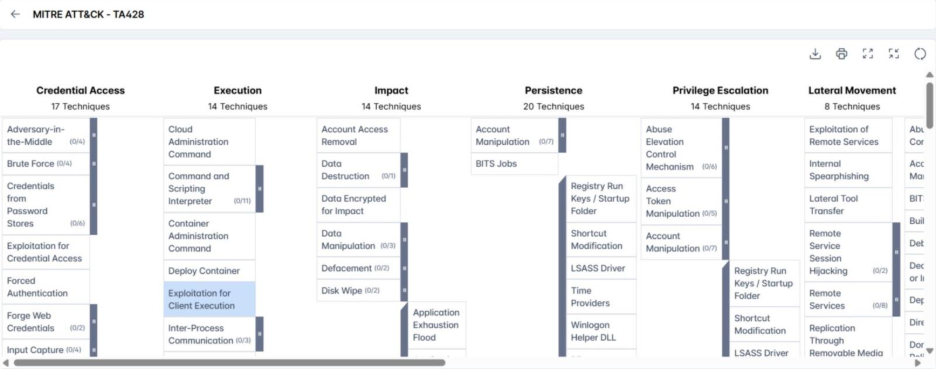
- Exploitation for Client Execution (T1203): Adversaries exploit vulnerabilities in client applications to execute arbitrary code, often targeting commonly used software because it increases the likelihood of successful compromise.
- User Execution (T1204): Adversaries rely on specific user actions to gain execution, using social engineering and phishing to trick victims into opening malicious files or links, with such actions frequently following initial access attempts.
- Boot or Logon Autostart Execution (T1547): Adversaries configure autostart mechanisms so programs run automatically at boot or user logon, maintaining persistence and creating opportunities to obtain higher privileges.
- Obfuscated Files or Information (T1027): Adversaries obfuscate or encrypt executables and files to make discovery and analysis harder, using compression, archiving, encryption, or encoding to evade detection across platforms and the network.
- OS Credential Dumping (T1003): Adversaries attempt to extract account credentials from the operating system or installed software, recovering password hashes or plaintext credentials for reuse.
- Screen Capture (T1113): Adversaries may capture screenshots of a victim’s desktop to collect visible information such as documents, credentials, or session content.