Emissary Panda, widely tracked under names such as APT27, Threat Group‑3390, ATK‑15, Bronze Union, Budworm, Earth, Smilodon, Group 35, Iron Taurus, Iron Tiger, LuckyMouse, Red Phoenix, TEMP.Hippo, TG‑3390, ZipToken, and other aliases are a long‑running Chinese‑attributed threat cluster that has been active since at least 2010. The group was last observed on 17‑Jul‑2025 and is primarily associated with targeted cyber‑espionage against strategic sectors and national‑level interests.
Emissary Panda conducts carefully planned intrusions focused on data theft and long‑term network access. The group’s operations emphasize strategic web compromises and watering‑hole campaigns: researchers attribute the compromise of more than 100 legitimate websites to Emissary Panda, deliberately selecting sites that the intended victims commonly visit.
In one documented campaign named Operation StealthyTrident, Emissary Panda collaborated with TA428 to broaden reach and effectiveness. A representative attack scenario would involve compromising a site visited by employees of a defense contractor, using that site to deliver exploits or malicious scripts, then planting webshells on SharePoint or other servers to siphon sensitive documents for espionage.
Geographic and Sector Focus

Emissary Panda’s origin is tracked to China (CN) with operational focus across the Asia & Pacific (APAC) region and beyond. The group has targeted organizations in a wide range of countries, including Australia, Canada, China, Germany, Spain, the United Kingdom, Hong Kong, Israel, India, Iran, Japan, South Korea, Mongolia, the Philippines, Russia, Thailand, Turkey, Taiwan, and the United States.
Industries commonly targeted include:
- Aerospace & defense
- Education
- Government and law enforcement agencies
- Manufacturing
- Technology and telecommunications
- Energy and related industrial sectors
The targeting pattern aligns with classic state‑level intelligence objectives: persistent access to technical blueprints, policy deliberations, and industrial processes.
Tooling and Malware Repertoire
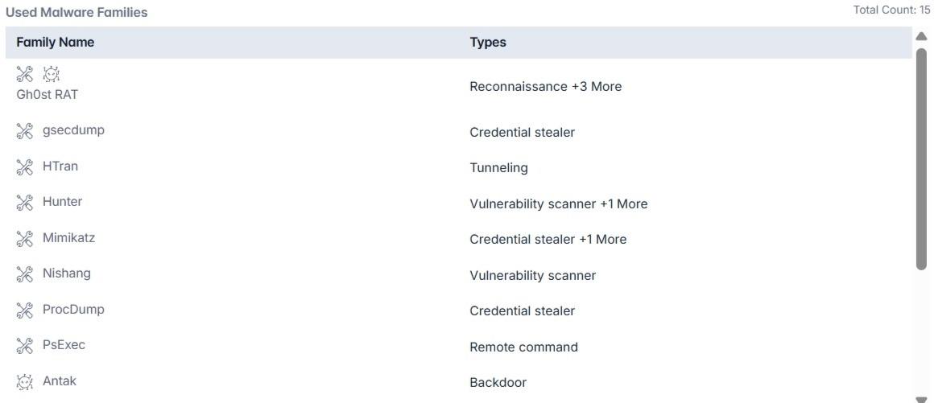
Emissary Panda’s toolkit comprises roughly 15 distinct malware families and common offensive utilities, mixing custom backdoors and widely available admin tools repurposed for intrusion and lateral movement. Notable families and utilities associated with the group include:
- Gh0st RAT: Remote access/reconnaissance family used historically for command‑and‑control and data collection.
- Gsecdump: A publicly available credential‑dumping tool (authored by TrueSec) that extracts Windows password hashes and LSA secrets; Emissary Panda uses the tool to harvest credentials for lateral movement and persistence.
- HTran: Tunneling utility used to proxy traffic or create covert channels.
- Hunter: Vulnerability scanner used to discover exploitable services (listed with other scanning behavior).
- Mimikatz: Credential harvesting utility commonly used to extract plaintext credentials and tokens.
- Nishang: Scripting-based tooling used for scanning and exploitation.
- ProcDump: A Sysinternals command‑line utility originally intended to capture process dumps; adversaries have abused ProcDump to capture in‑memory payloads and exfiltrate sensitive process data.
- PsExec: Legitimate Sysinternals remote execution tool used by operators to run commands and binaries on remote systems during lateral movement.
- Antak: An ASP.NET webshell (named after a mythological figure) that operates in concert with PowerShell to execute commands, move files, and maintain remote control on compromised servers.
- ASPXSpy, China Chopper, HTTPBrowser, HyperBro, PolPo, Unidentified_080: Assorted webshells, backdoors, and RATs. HyperBro deserves particular mention as a custom in‑memory backdoor used by TG‑3390: it typically consists of a signed loader, a malicious DLL loader, and an encrypted payload with hardcoded C2; operators deploy it as a final‑stage RAT with anti‑detection launchers and decompression/decoding routines.
How They Gain and Expand Access
Emissary Panda uses several techniques to gain initial access to targeted systems. These include taking advantage of exposed remote access services like VPNs, remote management tools, or container platforms, often using stolen login credentials.
They also rely on drive-by compromises, where users are tricked into visiting compromised websites that quietly deliver malware through the browser. In some cases, they exploit vulnerabilities in publicly accessible applications or services to break into networks.
Another method involves tampering with software supply chains, infecting tools, or updates before they reach the victim. Once inside a system, the group often steals passwords, executes commands remotely, and installs hidden backdoors to maintain control and move across the network, collecting valuable data along the way.
Operational Notes and Implications
Operators favor long‑lived footholds and data collection over short‑term disruptive actions; however, the presence of in‑memory loaders and sophisticated RATs such as HyperBro indicates capability for stealthy, resilient operations. The abuse of legitimate administrative tools (ProcDump, PsExec) and public utilities complicates detection; activities may appear benign unless telemetry is correlated and anomalous uses are flagged.
Conclusion
Protecting against advanced actors like Emissary Panda requires a proactive, layered cybersecurity strategy. Organizations should patch exposed systems, monitor admin tool usage, and stay alert to tactics like watering-hole attacks and supply chain compromises. Given the group’s global reach and persistence, traditional defenses alone aren’t enough.
Cyble’s AI-native platform offers a powerful edge, delivering real-time threat intelligence, early attack prediction, and automated response. Recognized by Gartner in 2025, Cyble’s tools, like BlazeAI and Cyble Vision, help organizations detect, respond to, and stay ahead of cyber threats like Emissary Panda.
Book a personalized demo with Cyble today and see next-generation cybersecurity in action.
Recommendations and Mitigations
- Patch and Update Regularly: Ensure all internet-facing applications, content management systems, and remote access services (VPNs, Citrix, remote management tools) are fully patched to reduce vulnerabilities.
- Monitor Administrative Tool Usage: Closely watch for unusual or unauthorized use of legitimate admin tools like PsExec, ProcDump, and Sysinternals utilities, which attackers often abuse for lateral movement and persistence.
- Implement Multi-Factor Authentication (MFA): Enforce MFA across all remote access points and sensitive systems to reduce the risk of credential compromise.
- Strengthen Credential Security: Use robust password policies and regularly audit for credential theft or misuse, employing tools to detect activities like credential dumping (e.g., Mimikatz, gsecdump).
- Detect and Analyze Webshell Activity: Continuously monitor web server and SharePoint logs for signs of webshells such as Antak, China Chopper, and ASPXSpy, which attackers use to maintain stealthy access.
- Reduce Attack Surface: Limit exposure of remote access services and container APIs by restricting access, applying least-privilege principles, and disabling unused services.
- Conduct Threat Hunting and Behavioral Analytics: Employ proactive threat hunting and anomaly detection to identify stealthy intrusions that leverage legitimate tools and in-memory malware like HyperBro.
- Secure Software Supply Chains: Implement rigorous controls and monitoring to prevent supply chain compromises that could introduce malicious code before software reaches deployment.
- Intelligence Sharing and Awareness: Stay informed about regional watering-hole attacks and emerging TTPs (tactics, techniques, and procedures) through trusted threat intelligence sources.
- Leverage AI-Powered Cybersecurity Platforms: Utilize advanced platforms like Cyble’s AI-native solutions for real-time threat intelligence, predictive analytics, automated detection, and rapid response to mitigate persistent threats such as Emissary Panda.
MITRE ATT&CK Techniques Associated with Emissary Panda

- External Remote Services (T1133): Emissary Panda exploits exposed remote access services such as VPNs, Citrix, Windows Remote Management, VNC, and container APIs to gain initial access or persistence, often using stolen credentials or abusing unauthenticated endpoints.
- Drive‑by Compromise (T1189): The group leverages compromised websites, injected JavaScript, modified script files in writable cloud storage, and malvertising to deliver browser exploits or steal application access tokens from visitors, frequently targeting sites popular with specific communities.
- Exploit Public‑Facing Application (T1190): Operators take advantage of vulnerabilities, misconfigurations, or software bugs in internet-facing applications, services, databases, and network devices to obtain footholds, escalate access, or move into cloud/container hosts.
- Supply Chain Compromise (T1195): Adversaries manipulate development tools, build environments, source repositories, dependencies, update mechanisms, system images, or distribution channels to insert malicious code prior to delivery and introduce compromises downstream.
- Compromise Software Supply Chain (T1195.002): The group specifically targets application software distribution and update channels—including popular open-source dependencies and installer paths—so that malicious code is delivered through legitimate updates or packages and activated against selected victims.
- Credential Dumping (T1003): Emissary Panda uses tools like Mimikatz and gsecdump to extract plaintext passwords, hashes, and tokens from compromised systems to escalate privileges and move laterally.
- Remote Services (T1021): The group employs legitimate remote execution tools such as PsExec and Windows Remote Management to execute commands and move laterally within a network.
- Web Shell (T1505.003): Operators deploy web shells like Antak, China Chopper, and ASPXSpy on compromised servers to maintain persistent remote access and execute arbitrary commands.
- Tunneling (T1572): Emissary Panda uses tunneling utilities such as HTran to create covert communication channels that proxy traffic and evade network detection.
- Vulnerability Scanning (T1595): The group utilizes tools like Hunter to scan networks and identify exploitable services or weaknesses for further exploitation and lateral movement.