Reaper — tracked by many names, including APT37, TA‑RedAnt, TEMP.Reaper and dozens of operation‑level aliases such as “Fractured Block,” “Operation ‘Are You Happy?’,” “Operation ‘Erebus’ and “Operation ‘Golden Time’ is a North Korean‑attributed threat actor that blends espionage and destructive malware operations.
The group was last observed on 17‑Jul‑2025 and is widely assessed as state‑sponsored. Its activity overlaps with other DPRK‑linked clusters such as Lazarus, and researchers routinely map a web of shared tooling, infrastructure, and objectives across those collections of aliases (for reference, other recorded synonyms include Cerium, Crooked Pisces, Geumseong121, InkySquid, Osmium, Red Eyes, Ricochet Chollima, Ruby Sleet, and many operation‑style labels).
Geographic and Sectoral Focus

Reaper’s primary focus is the Korean Peninsula — South Korea in particular — but its operations extend across the Asia‑Pacific region and beyond. Observed target countries include South Korea, Japan, and Vietnam, as well as China, Hong Kong, India, Nepal, Russia, Kuwait, Poland, Romania, the Czech Republic, the United Kingdom, and the United States.
Industry targeting is broad and purposefully strategic: aerospace and defense, automotive, chemicals, manufacturing, healthcare, education, government and law enforcement, media and entertainment, finance (BFSI), transportation and logistics, and technology are all reported victims or high‑value targets.
Operational Tradecraft and Distribution Vectors
Reaper combines social engineering with technical opportunism. The group commonly uses spear‑phishing, malicious attachments, strategic web compromises, and opportunistic drive‑by compromises to deliver initial payloads.
Researchers have documented distribution via compromised websites, torrent and file‑sharing sites, and weaponized documents specifically exploiting applications common in the region — most notably Hangul Word Processor and, historically, Adobe Flash — including use of zero‑day vulnerabilities.
Victims may be enticed by convincing lures, and actors are known to embed multiple stages in decoy documents so that shellcode decrypts and retrieves secondary payloads.
Command, Control, and Operational Security
Reaper demonstrates deliberate C2 camouflage and opportunistic use of third‑party services. The group has used compromised servers, public messaging platforms, and cloud providers for command and control.
A notable example is BLUELIGHT, a remote access Trojan first observed in early 2021 that leverages cloud services such as Microsoft Graph API for C2. BLUELIGHT authenticates using hardcoded parameters and OAuth2 tokens to establish communication channels — a deliberate tactic to weaponize legitimate infrastructure and hinder detection. In several campaigns, BLUELIGHT has been paired with other espionage malware such as RokRAT.
Malware Repertoire
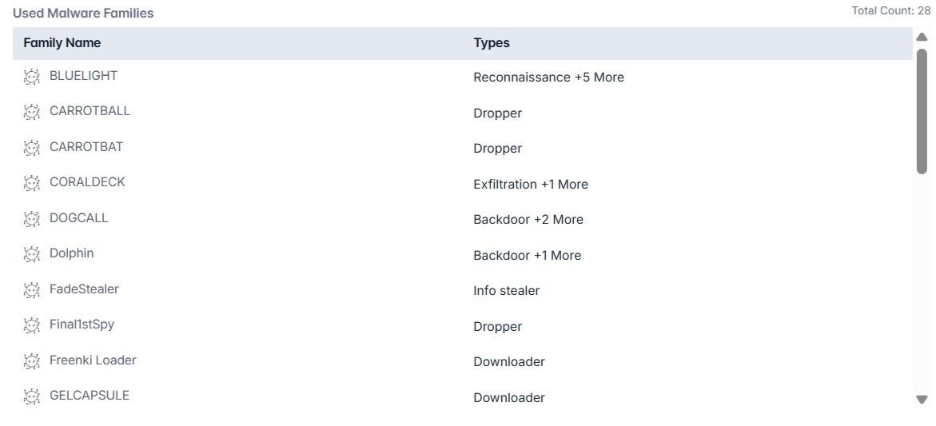
Analysis attributes 28 distinct malware families to Reaper activity. The list includes droppers, loaders, backdoors, reconnaissance tools, info‑stealers, credential stealers, exfiltration tools, a ransomware family (Erebus), and at least one wiper (RUHAPPY). Representative families and observed behaviors:
- BLUELIGHT: A cloud‑abusing RAT that uses Microsoft Graph API and OAuth2 authentication with hardcoded parameters for C2; employed for persistent espionage and paired with other tooling.
- CARROTBALL: An FTP downloader documented by Unit 42 in late 2019; used to deploy SYSCON (a RAT) via spear‑phishing lures.
- CARROTBAT: Associated with the “Fractured Block” campaign; reported to have circulated 29 unique samples containing decoy documents since March of this year and to deliver payloads such as Syscon and Oceansalt.
- CORALDECK: An exfiltration utility that collects files and packages them in password‑protected archives (RAR/ZIP/WinImage) before HTTP POST exfiltration using hardcoded headers.
- DOGCALL: A Hangul Word Processor exploit‑delivered backdoor targeting government and military entities; capable of screenshots, keylogging, VM‑sandbox detection, and cloud storage abuse (Cloud, Box, Dropbox, Yandex). Some DOGCALL‑infected systems have also shown deployment of the RUHAPPY wiper, demonstrating destructive capability alongside espionage.
- FadeStealer: A comprehensive surveillance tool that performs real‑time keylogging, periodic screenshots, audio recording, monitoring of USB/MTP devices, and packages collected data into timestamped, password‑protected RAR archives for HTTP POST exfiltration.
- Other families include CARROTBAT/CARROTBALL variants, Dolph in, GOLDBACKDOOR, N1stAgent, Nokki, Oceansalt, SHUTTERSPEED, SLOWDRIFT, SOUNDWAVE, ZUMKONG (credential stealer), MILKDROP (loader), WINERACK, and Erebus (ransomware), among others.
Conclusion
Reaper is a technically advanced and regionally focused threat actor that combines espionage with destructive tactics like ransomware and wipers. Its use of cloud APIs for command-and-control, exploitation of native document vulnerabilities, and a diverse malware arsenal poses cybersecurity risks to organizations across the Asia-Pacific and allied regions.
To defend against such threats, organizations should focus on patching document processors and browser plugins, enhancing email security against spear-phishing, monitoring suspicious scheduled tasks and cloud API activity, and developing incident response plans for both espionage and destructive attacks.
Cyble, a leader in AI-driven cybersecurity, provides advanced threat intelligence and autonomous defense through its BlazeAI platform, recognized by Gartner and other top analysts. By using Cyble’s AI-native solutions, organizations can better predict, detect, and neutralize threats like Reaper.
Schedule a personalized demo with Cyble today to experience next-generation cybersecurity in action.
Recommendations and Mitigation
- Regularly patch document processors, browsers, and plugins to close exploitable vulnerabilities.
- Implement advanced email filtering and user training to defend against spear-phishing attacks.
- Monitor for unusual scheduled tasks, process behavior, and cloud API communications.
- Implement endpoint detection and response tools to identify multi-stage and fileless malware.
- Enforce least privilege and network segmentation to limit lateral movement.
- Watch for data exfiltration using password-protected archives and abnormal HTTP traffic.
- Develop and test incident response plans covering both espionage and destructive malware.
- Maintain secure, offline backups to enable recovery from ransomware and wiper attacks.
- Use AI-driven threat intelligence platforms like Cyble BlazeAI for proactive threat prediction and response.
- Participate in cyber threat intelligence sharing to stay updated on Reaper’s tactics and indicators.
MITRE ATT&CK Techniques Associated with Reaper
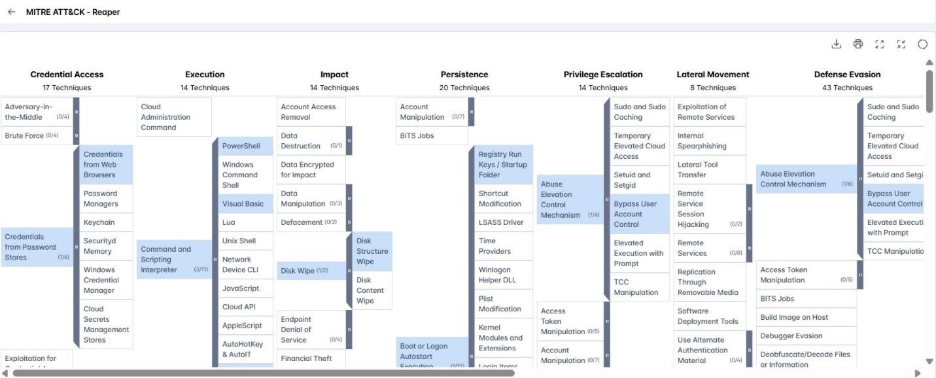
MITRE ATT&CK Techniques (Source: Cyble Vision)
- Drive‑by Compromise (T1189): Reaper leverages compromised websites, torrent/file‑sharing pages, and malvertising to deliver browser or plugin exploits and lure victims.
- Exploitation for Client Execution (T1203): The group exploits vulnerabilities in client applications such as Hangul Word Processor and legacy plugins (e.g., Flash), including zero‑days, to gain code execution.
- Phishing (T1566): Adversaries send deceptive emails and messages to trick recipients into visiting malicious sites or executing payloads.
- Spearphishing Attachment (T1566.001): Reaper delivers multi‑stage malware via targeted email attachments (Office docs, PDFs, archives) that require user interaction.
- User Execution (T1204): The actor relies on social engineering to induce users to open files, enable active content, or install remote‑access tools.
- Scheduled Task/Job (T1053): Attackers create OS scheduled jobs to ensure recurring or startup execution of malicious code for persistence.
- Scheduled Task (Windows) (T1053.005): Reaper abuses Windows Task Scheduler (schtasks, API wrappers) and hides tasks via registry tweaks to mask persistent payloads.
- Command and Scripting Interpreter (T1059): The group uses interpreters (CMD, Bash, Python, etc.) to run scripts and orchestrate payload stages.
- PowerShell (T1059.001): Reaper uses PowerShell to execute commands, download and run payloads in memory, and interact with cloud APIs for C2.
- Visual Basic / VBA (T1059.005): Adversaries embed VBA or VBScript in documents to automate malicious execution and evade simple controls.
- Dynamic Data Exchange (T1559.002): The actor can weaponize DDE in Office documents to execute commands without relying on macros.
- Native API (T1106): Reaper leverages native OS APIs and syscalls to spawn processes, load modules, and evade user‑mode hooks.