Energetic Bear is a Russia-based, state-sponsored threat group with known affiliations to the GRU. The group is widely tracked across the cybersecurity landscape under various aliases. Common designations include ATK 6, Blue Kraken, Bromine, Crouching Yeti, Dragonfly, Electrum, Ghost Blizzard, Group 24, ITG15, Iron Liberty, Koala Team, and TG-4192.
Active since at least 2011, Energetic Bear primarily targets critical infrastructure, with a strong focus on industrial control systems (ICS) in the energy sector. Its campaigns blend espionage and disruption, consistently emphasizing stealth, long-term access, and persistent surveillance within compromised networks.
The group’s operations encompass a wide range of techniques, including watering hole attacks, supply chain compromises, and spear-phishing campaigns. These are often used to infiltrate trusted environments, such as legitimate websites or software distribution platforms, to deliver malware capable of harvesting credentials and gaining unauthorized access.
Energetic Bear also uses the injection of credential-stealing malware into compromised web portals. Once inside, the attackers pivot laterally within the network, deploying backdoors and manipulating ICS components. Their tactics enable them to maintain long-term access, conduct surveillance, and, in more extreme scenarios, launch sabotage operations, such as interfering with energy distribution, disabling power infrastructure, or intercepting critical communications across targeted systems.
Geographic Scope

Energetic Bear has operated across a wide geographic footprint, with its primary targets concentrated in Europe and the United Kingdom. Countries frequently affected by the group’s activities include Germany, France, Spain, the United Kingdom, Poland, Romania, Italy, Norway, Greece, Bulgaria, Serbia, Turkey, and Ukraine.
In North America, Canada has been identified as a key target, while in the Asia-Pacific region and beyond, attacks have also been observed in Australia and Russia itself, suggesting both external and internal targeting capabilities.
The group has consistently focused on sectors critical to national security, infrastructure resilience, and technological innovation. These include industries such as Energy and Utilities, Aerospace and Defense, Pharmaceuticals and Biotechnology, Information Technology and IT-enabled Services (IT & ITES), Education, Construction, and Manufacturing.
Tactics, Techniques & Tools
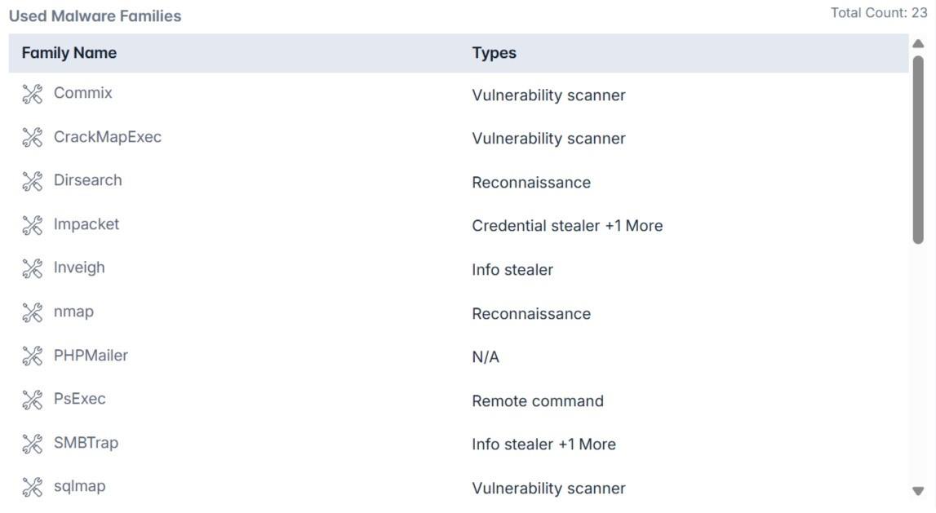
Energetic Bear has employed a wide array of reconnaissance, execution, persistence, and data exfiltration tools. Their known toolkit includes 23 malware families and offensive security tools, many of which are open-source utilities reappropriated for malicious operations.
| Name | Function | Category |
| Commix | OS command injection | Vulnerability Scanner |
| CrackMapExec | AD exploitation, lateral movement | Post-Exploitation Tool |
| Dirsearch | Directory brute-forcing | Reconnaissance |
| Impacket | Credential theft, remote execution | Credential Stealer |
| Inveigh | LLMNR spoofing, MITM | Info Stealer |
| Nmap | Host/service enumeration | Reconnaissance |
| PHPMailer | Email abuse | Exploitation Tool |
| PsExec | Remote command execution | Remote Admin Tool |
| SMBTrap | SMB traffic logging | Info Stealer |
| Sqlmap | SQL injection automation | Vulnerability Scanner |
| Subbrute | Subdomain brute-forcing | Reconnaissance |
| Sublist3r | OSINT-based subdomain enumeration | Reconnaissance |
| Wpscan | WordPress vulnerability scanning | Vulnerability Scanner |
| Dorshel | Trojanized software delivery | Backdoor |
| Goodor | Covert access tool | Backdoor |
| Havex RAT | ICS exploitation, remote access | ICS Malware |
| Heriplor | Persistent backdoor | Backdoor |
| Industroyer | Industrial systems targeting | ICS Malware |
| Karagany | Modular espionage platform | Backdoor |
| Listrix | Enumeration & data collection | Recon Tool |
| Sysmain | Network scanning and enumeration | Recon Tool |
| Hello EK | Browser-based delivery | Exploit Kit |
| LightsOut EK | Malware loader | Loader |
Energetic Bear to escalate privileges, map Active Directory environments, dump credentials, and move laterally within large enterprise networks.
Threat Assessment
Energetic Bear remains one of the most dangerous ICS-focused adversaries in the cyber domain. While much of their activity involves traditional espionage, credential harvesting, network mapping, and long-term access, they also possess disruption capability.
Their malware catalog (e.g., Havex, Industroyer) has previously been used against energy distribution networks.
Conclusion
Energetic Bear is a high-impact, GRU-linked threat actor known for targeting critical infrastructure, especially in the energy and defense sectors, using a mix of custom malware and open-source tools. Their ability to infiltrate and manipulate industrial control systems positions them as a serious geopolitical threat, with capabilities extending well beyond traditional espionage.
To counter advanced actors like Energetic Bear, organizations need proactive, intelligence-led defense. Cyble, the world’s first AI-native, intelligence-driven cybersecurity platform, offers exactly that. With solutions like Blaze AI, Vision, and Titan, Cyble delivers real-time threat detection, predictive analytics, and autonomous response. Recognized by Gartner and trusted globally, Cyble enables security teams to outpace today’s most advanced adversaries.
Schedule a free demo today to find out more about Cyble!
Recommendations and Mitigation
Organizations operating in targeted sectors should adopt a layered security strategy focused on visibility, segmentation, and threat detection:
- Implement network segmentation to isolate ICS/OT environments from IT infrastructure.
- Block known malicious IPs and monitor SMB traffic for anomalies.
- Conduct regular audits of remote execution tools (PsExec, WinRM, etc.).
- Harden public-facing assets with WAFs and updated CMS/plugin patches.
- Use AI-driven EDR/XDR solutions to detect lateral movement and credential theft.
- Limit PowerShell and scripting tool use to admin-only environments.
- Train employees on phishing awareness and waterhole attack scenarios.
Known TTPs (Mapped to MITRE ATT&CK)
While not explicitly listed in the original data, based on tooling and behaviors, Energetic Bear aligns with the following MITRE ATT&CK TTPs:
- T1059 – Command and Scripting Interpreter
- T1021.002 – Remote Services: SMB/Windows Admin Shares
- T1203 – Exploitation for Client Execution
- T1566.002 – Spearphishing Link
- T1189 – Drive-by Compromise (Watering Hole)
- T1210 – Exploitation of Remote Services
- T1046 – Network Service Scanning
- T1071 – Application Layer Protocol: Web
Observed Infrastructure & IOCs
| IOC | First Seen | Last Seen | IP/Hash Type | Risk Score |
| 95db15c67b48945237af7de61f3dbab92c99edd1 | 06-Sep-2017 | 22-Sep-2025 | File Hash (SHA1) | 70 (Medium) |
| 108.177.235.92 | 23-Oct-2020 | 22-Sep-2025 | IP Address | 70 (Medium) |
| 138.201.186.43 | 23-Oct-2020 | 22-Sep-2025 | IP Address | 70 (Medium) |
| 146.0.77.60 | 23-Oct-2020 | 22-Sep-2025 | IP Address | 70 (Medium) |
| 149.56.20.55 | 23-Oct-2020 | 22-Sep-2025 | IP Address | 70 (Medium) |
| 184.154.150.66 | 06-Sep-2017 | 22-Sep-2025 | IP Address | 70 (Medium) |
| 193.37.212.43 | 23-Oct-2020 | 22-Sep-2025 | IP Address | 70 (Medium) |
| 195.16.88.6 | 12-Jun-2017 | 22-Sep-2025 | IP Address | 70 (Medium) |
| 212.252.30.170 | 23-Oct-2020 | 22-Sep-2025 | IP Address | 70 (Medium) |
| 213.74.101.65 | 23-Oct-2020 | 22-Sep-2025 | IP Address | 70 (Medium) |