Turla, one of the most enduring and elusive state-sponsored cyber threat groups, has been a persistent presence on the global espionage landscape since 2004. Attributed to Russia and closely tied to the Federal Security Service (FSB), Turla has executed a broad range of espionage campaigns, primarily targeting government, military, and defense organizations across dozens of countries. The group was last observed on July 29, 2025, continuing its operations with a mix of stealth, deception, and technical prowess.
Turla is known under a sprawling list of aliases, including APT 28, Belugasturgeon, Blue Python, Iron Hunter, Krypton, Wraith, Waterbug, Venomous Bear, and Pensive Ursa. It has also been linked to named campaigns such as Operation Epic Turla, Satellite Turla, Moonlight Maze, WITCHCOVEN, and Turla Mosquito. These aliases reflect the evolving threat landscape and the attribution difficulties that come with it.
Geopolitical Footprint

While Russia remains its origin point, Turla’s targeting patterns span a wide global spectrum. Its victims include organizations and institutions in Afghanistan, Azerbaijan, Belarus, Bolivia, Botswana, Chile, China, Denmark, Egypt, Estonia, Greece, India, Kazakhstan, Kyrgyzstan, Latvia, Mexico, Nepal, Pakistan, Poland, Qatar, Russia, Spain, the USA, and more than 30 other countries.
These countries share one commonality: strategic value, either political, military, or economic, making them ideal targets for state-sponsored cyber espionage.
Tactics, Techniques, and Procedures (TTPs)
Turla’s operations are carefully planned and involve multiple layers of intrusion. The group often begins by gaining access to its victims through a combination of deceptive websites and targeted emails. In some cases, it has compromised legitimate websites that its targets regularly visit, quietly injecting malicious software into these trusted pages.
In others, they send convincing emails with links that appear to lead to well-known and reputable domains, tricking recipients into downloading harmful files.
Once access is gained, Turla uses various techniques to launch and control its malicious programs. These may include automated scripts, system commands, or specially crafted tools to execute their code and maintain control over the infected systems. In many cases, Turla relies on common scripting languages and utilities to stay hidden and avoid detection.
The group has also been known to take advantage of built-in system functions to bypass security protections and run commands secretly. To maintain their presence inside a network over long periods, they often exploit local user accounts, especially those with shared or reused passwords across multiple systems, allowing them to quietly move through a network without raising suspicion.
Malware Arsenal

Turla’s toolset is massive and spans across multiple platforms (Windows, Linux, and macOS). Their malware library includes custom-developed backdoors, loaders, credential stealers, reconnaissance tools, droppers, and rootkits. Some of the notable malware families used by the group include:
- Backdoors: Agent.BTZ, ComRAT, Kazuar, Neuron, Gazer, Penquin Turla, TinyTurla, Mosquito, CloudDuke, Epic, PowerStallion, Cobra Carbon System.
- Credential Stealers: Mimikatz, pwdump, LightNeuron.
- Recon Tools: nbtstat, SScan, Systeminfo, IcedCoffee, KopiLuwak, WITCHCOVEN, Topinambour.
- Loaders and Droppers: DoublePulsar, Meterpreter, NetFlash, NewPass, WhiteAtlas.
Additionally, Turla has integrated powerful zero-day exploits into its campaigns, such as EternalBlue and EternalRomance. Their arsenal also includes lesser-known tools like MiamiBeach, Pelmeni, TurlaRPC, Unidentified ASP 001, and MiniPocket, some of which remain partially analyzed by the cybersecurity community.
Conclusion
Turla exemplifies the modern-day state-sponsored cyber threat, with stealthy, persistent, and highly technical prowess. With a history spanning nearly two decades, this group has consistently demonstrated its ability to infiltrate critical networks, remain undetected, and conduct long-term espionage across global targets.
Traditional defenses are no longer enough to combat these groups. Organizations need intelligence-driven, AI-native security that moves faster than the adversary.
Cyble delivers exactly that.
Recognized by leading analysts and trusted by governments and enterprises worldwide, Cyble’s platforms, powered by Blaze AI, offer predictive threat intelligence, autonomous response, and unmatched visibility.
To stay ahead of today’s most advanced threat actors, including Turla, security teams must move from reactive to proactive.
Cyble makes that shift possible.
Book your free demo today.
Mitigation and Recommendations
- Use advanced email filters to block spear-phishing emails.
- Train employees to identify phishing links and fake websites.
- Enable multi-factor authentication (MFA) for all accounts.
- Disable unused or shared local accounts across networks.
- Restrict PowerShell and scripting tools to admin use only.
- Patch systems regularly, especially for high-risk vulnerabilities.
- Monitor web activity to block access to known bad sites.
- Deploy EDR tools to detect and respond to suspicious behavior.
- Segment networks to limit lateral movement by attackers.
- Use AI-driven threat intelligence (like Cyble Vision and Blaze AI) for early detection and automated response.
MITRE ATT&CK Techniques Associated with Turla
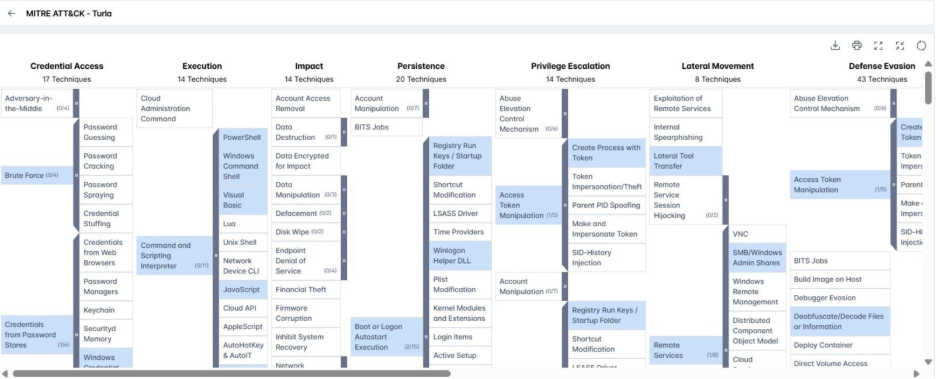
- Drive-by Compromise (T1189): Turla has infected victims by compromising legitimate websites that are frequently visited, injecting malware silently (watering hole attacks).
- Spearphishing via Link (T1566.002): Turla has lured users into downloading malware by sending phishing emails containing malicious links disguised as trusted domains.
- PowerShell (T1059.001): Turla uses PowerShell scripts to execute malware in memory and run commands, sometimes using custom tools like Empire’s PSInject.
- Windows Command Shell (T1059.003): Turla’s backdoors often rely on cmd.exe to issue system-level commands after gaining access.
- Visual Basic (T1059.005): VBS scripts automate tasks and deploy payloads across various operations.
- Python (T1059.006): IronPython scripts are used as part of Turla’s custom toolchain (IronNetInjector) to drop and execute malicious components.
- JavaScript (T1059.007): Turla uses custom JavaScript-based backdoors for execution and system control.
- Native API (T1106): Turla employs direct API calls to bypass defenses like AMSI and execute malicious actions through system-level functions or named pipes.