Overview
Stone Panda (also known by several other names, such as APT 10, Bronze Riverside, Cicada, and others) is an advanced persistent threat (APT) group attributed to state-sponsored activities originating from China. This group, often associated with the Tianjin bureau of the Chinese Ministry of State Security (MSS) and Huaying Haitai, has been active for many years, with its most recent operation observed as of July 16, 2025.
Stone Panda has been notorious for targeting a wide range of sectors, including healthcare, defense, aerospace, government agencies, media, and academic institutions. Their primary motivation is espionage, and they use various methods to gain unauthorized access to sensitive data, intellectual property, and confidential information.
Alternative Names for Stone Panda
Stone Panda operates under many aliases, including:
- APT 10
- ATK 41
- Bronze Riverside
- CTG-5938
- CVNX
- Cicada
- Cuckoo Spear
- Earth Kasha
- Granite Taurus
- Happyyongzi
- Hogfish
- ITG01
- Potassium
- Red Apollo
- TA429
- menuPass
- menuPass Team
Targeted Regions and Countries
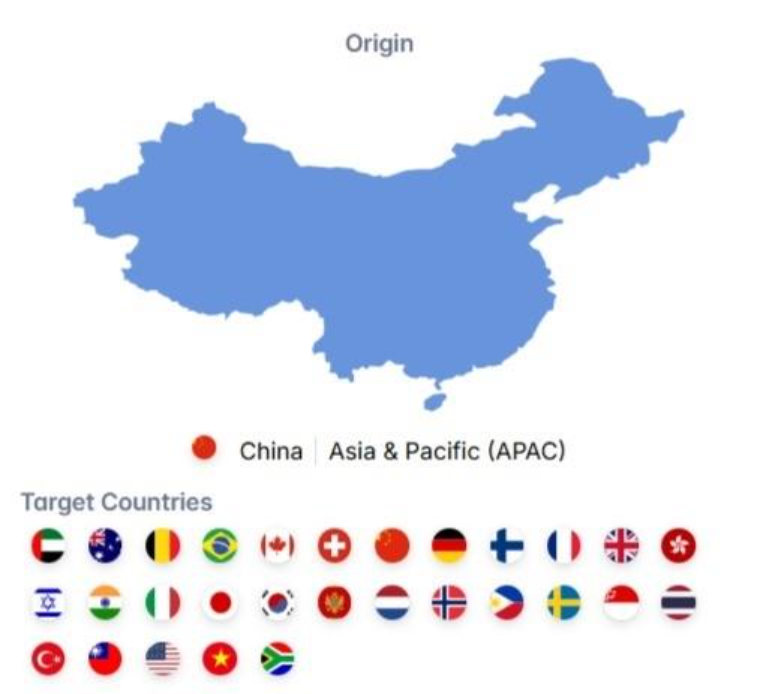
Stone Panda is a globally active threat actor, focusing its attacks on a variety of countries across different continents. Their operations have spanned regions such as Asia, Europe, and North America, with notable targeting of countries like:
- United States
- United Kingdom
- Japan
- Germany
- South Korea
- India
- Brazil
- Canada
- Israel
- Turkey
- China (interestingly, they also target their home country for various purposes)
Additionally, countries like the United Arab Emirates, Switzerland, Mexico, Vietnam, Sweden, and others have been victims of their campaigns.
Tactics, Techniques, and Procedures (TTPs)
Stone Panda uses a variety of cybersecurity techniques to achieve their goals. Their initial access typically involves spear-phishing emails, which carry malware-laden attachments or links. They often exploit vulnerabilities in public-facing applications, such as Pulse Secure VPNs, to hijack active sessions. Managed Service Providers (MSPs) are also used as trusted entry points for their attacks, where Stone Panda utilizes these relationships to infiltrate their target networks.
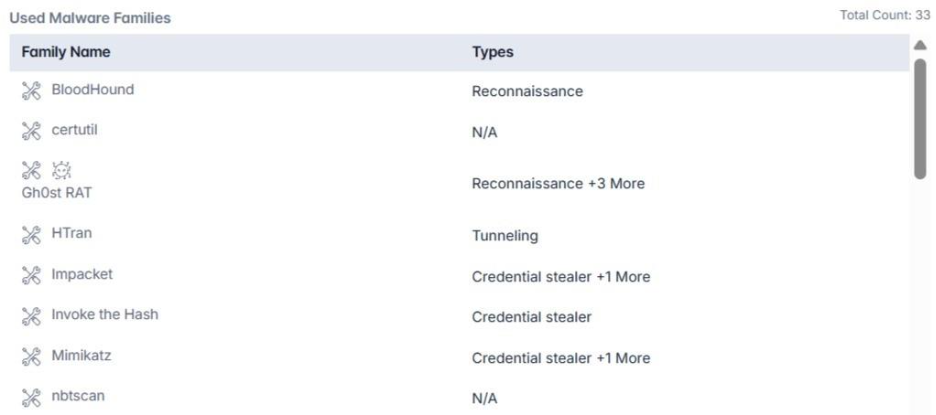
Once inside a system, Stone Panda uses various malware families to execute commands, steal credentials, maintain persistence, and escalate privileges. These tools and malware families include:
- BloodHound: An Active Directory reconnaissance tool, BloodHound helps Stone Panda map out attack paths by revealing relationships within Active Directory (AD) environments. This tool is crucial for privilege escalation during attacks.
- Impacket: A Python toolset for network protocol manipulation, allowing attackers to perform network reconnaissance, dump credentials, and exploit vulnerabilities in systems like Kerberos.
- Mimikatz: A tool for extracting plaintext passwords, Kerberos tickets, and other credential information from Windows systems. Stone Panda often uses Mimikatz to escalate privileges and gain further access across networks.
- PowerSploit: An offensive security framework used to execute code, maintain persistence, and bypass security controls within compromised environments.
- PowerView: Part of the PowerSploit framework, PowerView helps attackers gain visibility into Windows domains, identify misconfigurations, and escalate privileges within the compromised network.
- HTran: Used for tunneling and obfuscating traffic, allowing the group to mask their activities and evade detection during their operations.
- QuasarRAT and Gh0st RAT: Remote access trojans (RATs) that allow attackers to control compromised machines remotely.
- Poison Ivy: A backdoor trojan commonly used by Stone Panda for maintaining persistence on compromised systems.
Other malware families used by the group include Derusbi, Anel, China Chopper, MiS-Type, and Rubeus, among others.
Malware and Tools in Action
- BloodHound helps uncover hidden paths to administrative privileges and is particularly effective in privilege escalation operations. For example, Stone Panda may use BloodHound to identify and exploit hidden admin accounts, granting them the ability to elevate privileges and move laterally within a network.
- Mimikatz is frequently used by Stone Panda to harvest credentials, allowing them to escalate privileges and expand their reach across a compromised network. Once credentials are obtained, they can move laterally to sensitive systems, stealing data or installing additional malicious tools.
- Impacket is used to manipulate Kerberos tickets, aiding in credential dumping and remote service execution. It can also manipulate Windows network protocols, allowing attackers to pivot and maintain access.
Techniques for Maintaining Persistence
Stone Panda deploys a number of tactics to ensure that their malicious payloads remain undetected and functional over time. These techniques include:
- Scheduled Tasks: Stone Panda creates tasks on compromised systems that automatically execute commands, allowing them to maintain a persistent foothold within the environment.
- Credential Reuse: The group often exploits legitimate user accounts shared by MSPs and clients, maintaining a low profile while moving within networks.
- DLL Hijacking and Side-loading: Stone Panda uses malicious DLLs to bypass security mechanisms and keep control of compromised systems.
- Process Hollowing: The group employs process hollowing to run malicious code within legitimate processes, allowing them to escalate privileges and hide their activities.
- Bypassing Digital Signatures: Stone Panda is known to tamper with digital certificates, allowing them to use malicious files that appear to be signed with legitimate certificates, thus evading detection.
Credential Access and Exfiltration
Stone Panda’s credential theft tactics include using tools like wmiexec.vbs and secretsdump.py to extract sensitive information from Active Directory databases and the SAM database. These tools effectively dump password hashes and other authentication details, which can then be used to escalate privileges and further infiltrate the network.
Once they have obtained the necessary credentials, Stone Panda’s attackers gain unrestricted access to critical systems, where they can exfiltrate data, implant additional malware, or prepare the system for future exploitation.
Notable Campaigns
Stone Panda has been involved in various high-profile cyber-espionage campaigns, often targeting organizations in the academic, defense, and pharmaceutical sectors. For example, they have been linked to attacks on Japanese academic institutions and pharmaceutical companies, aiming to steal intellectual property and sensitive research data.
Their spear-phishing campaigns often involve carefully crafted emails with malicious attachments designed to exploit specific vulnerabilities in their targets’ systems. The COVID-19 pandemic saw an increase in Stone Panda’s activity, particularly targeting organizations involved in healthcare and vaccine research.
Conclusion
Stone Panda remains one of the most advanced and persistent state-sponsored APT groups, with global operations focused on espionage, intellectual property theft, and strategic disruption. Their techniques, from spearphishing and credential theft to stealthy malware, make them a major cybersecurity threat.
To counter such adversaries, organizations need more than just basic defense; they need proactive, intelligent security.
Cyble, recognized by Gartner in multiple 2025 Hype Cycles, leads the way with the world’s first AI-native, intelligence-driven cybersecurity platform. Powered by BlazeAI, Cyble predicts, detects, and neutralizes threats before they strike.
Experience true autonomous cybersecurity.
Book a free demo with Cyble today.
Mitigations and Recommendations
- Implement Multi-Factor Authentication (MFA): Prevent unauthorized access by securing all accounts, especially those used by MSPs and administrators, with MFA.
- Patch Public-Facing Applications Promptly: Apply updates to VPNs, web servers, and other internet-facing assets (e.g., Pulse Secure VPN) to prevent exploitation of known vulnerabilities.
- Restrict PowerShell and WMI Usage: Only trusted administrators should have access to scripting tools like PowerShell and WMI, and script execution should be monitored closely.
- Network Segmentation and Least Privilege: Divide critical assets into isolated network segments and enforce strict access controls to limit lateral movement.
- Deploy Endpoint Detection and Response (EDR): Use advanced EDR solutions to detect tools like Mimikatz, Impacket, and BloodHound. Look for behaviors like process hollowing and credential dumping.
- Monitor for Unusual Scheduled Tasks and DLL Activity: Regularly audit scheduled tasks and DLL loading behavior to catch persistence mechanisms such as DLL hijacking and side-loading.
- Harden Active Directory Environments: Use tools like Microsoft LAPS, disable unnecessary accounts, and monitor for suspicious AD enumeration attempts.
MITRE Attack Techniques Associated with Stone Panda

- Exploit Public-Facing Application (T1190): Exploited vulnerabilities in Pulse Secure VPNs to hijack sessions.
- Trusted Relationship (T1199): Used legitimate access via Managed Service Providers (MSPs) to infiltrate target environments.
- Spearphishing Attachment (T1566.001): Sent malicious Office documents and executables disguised as documents via email in spearphishing campaigns.
- Windows Management Instrumentation (T1047): Used a modified wmiexec.vbs script for remote command execution via WMI.
- PowerShell (T1059.001): Leveraged PowerSploit to inject shellcode into PowerShell sessions.
- Windows Command Shell (T1059.003): Executed commands through CLI and reverse shells; used malicious macros in Office docs.
- Native API (T1106): Called native Windows APIs like GetModuleFileName, lstrcat, CreateFile, and ReadFile.
- Malicious File (T1204.002): Sent Windows Shortcuts or Office documents via spearphishing to entice users into execution.
- Scheduled Task (T1053.005): Created scheduled tasks using scripts to maintain persistence on victim machines.
- Valid Accounts (T1078): Used legitimate shared credentials (e.g., between MSPs and clients) to maintain access.
- DLL Search Order Hijacking (T1574.001): Hijacked DLL loading sequences to execute malicious code.