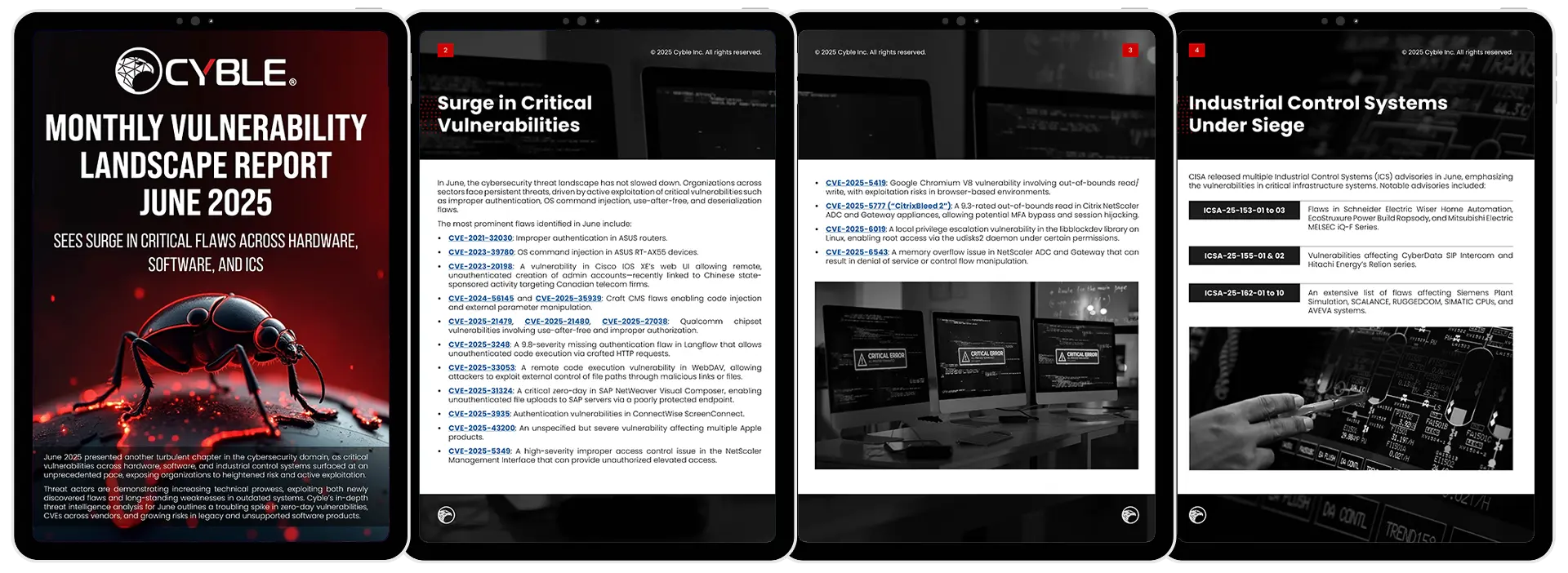
Critical Vulnerabilities Surge Across IT and ICS Systems
June 2025 brought a wave of high-severity vulnerabilities impacting core infrastructure—from consumer routers to enterprise software and critical ICS components. Cyble’s Monthly Vulnerability Landscape Report breaks down the most exploited CVEs, highlights zero-day trends, and reveals attacker behaviors from both surface web and underground sources.
Why This Report Matters
- Track High-Risk Vulnerabilities
Get detailed insights into 20+ critical CVEs, including flaws in ASUS, Cisco, Citrix, Apple, SAP, and more, that are actively being exploited in the wild. - Analyze ICS Attack Vectors
Understand industrial vulnerabilities impacting Schneider Electric, Siemens, and Mitsubishi Electric, as flagged in June’s CISA advisories. - Detect Zero-Day Trends
Discover which vendors—including Qualcomm, Microsoft, and Google—were affected by zero-days in June and what it means to your security posture. - Spot Weaknesses in Legacy Systems
Learn how unsupported software and EOL systems continue to introduce serious risks, including hardcoded credentials and local privilege escalation flaws.
The June 2025 vulnerability snapshot reinforces the need for real-time visibility, fast response, and proactive vulnerability management. With attackers exploiting both modern and legacy systems, security teams must stay agile.
Cyble’s threat intelligence solutions provide 24/7 visibility into vulnerabilities, exposed assets, and threat actor behavior, empowering enterprises to detect, defend, and respond faster than ever.